Why 24/7 Network Monitoring Is the Silent Guardian of Your Business

Why 24/7 Network Monitoring Is the Silent Guardian of Your Business
Your network isn’t just IT infrastructure — it’s the backbone of your business. In healthcare, finance, education, or SaaS, every second of downtime or data loss can trigger compliance violations, lost revenue, or reputational damage.
Yet most organizations still treat network monitoring as an afterthought. Legacy tools send alerts after something breaks, but by then the damage is already done. Downtime costs $5,600 per minute (Gartner) — a price few organizations can afford.
At Protected Harbor, we don’t just watch for problems. We own the stack, rebuild fragile systems, and deliver proactive monitoring that turns your network into a business guardian — not a liability.
————————————————————————————————————————————————————————————————————————
The Illusion of Visibility: Why Most Network Monitoring Fails
Many businesses believe that having a basic monitoring tool in place means they’re covered. They assume that because they receive alerts when something goes down, they’re ahead of the game. This is the first trap.
Legacy monitoring systems often provide a false sense of security, implementing reduce network downtime. They might tell you when a server is offline, but they won’t warn you about:
- Performance degradation that’s slowly choking your critical applications
- Security anomalies that indicate an attacker is already inside your network
- Capacity issues that will lead to downtime in the coming weeks
“Most network monitoring tools are like rearview mirrors – they show you where you’ve been, not where you’re headed. By the time you see the problem, you’re already crashing.” —Protected Harbor
Traditional monitoring approaches are fundamentally reactive. They wait for something to break before sounding the alarm. In today’s environment, where downtime can cost $5,600 per minute (Gartner), this approach is not just inadequate – it’s dangerous.
————————————————————————————————————————————————————————————————————————
The Hidden Risks of Inadequate Network Monitoring
A poorly monitored network isn’t just an IT problem – it’s a business crisis waiting to happen. For organizations in regulated industries, the consequences can be severe:
1. Security Blind Spots
Without comprehensive visibility, threats can move freely through your network. We’ve seen:
- Unpatched devices running critical applications that haven’t been updated in years
- Unauthorized access pointscreated by well-meaning employees trying to “work around” IT limitations
- Data exfiltration happening through legitimate channels that never trigger alerts
In healthcare or financial environments, these gaps can lead directly to HIPAA or PCI-DSS violations, with fines reaching millions of dollars.
2. Performance Bottlenecks
Network performance issues rarely announce themselves with dramatic crashes. Instead, they manifest as:
- Gradual slowdowns that reduce employee productivity by 20-40%
- Intermittent connectivity that frustrates users and damages customer experiences
- Application timeouts that force staff to develop inefficient workarounds
These issues are particularly damaging for SaaS companies and educational institutions, where user experience directly affects retention and success.
3. Compliance Gaps
Most regulatory frameworks require detailed logging and monitoring capabilities. Without proper network monitoring, organizations:
- Cannot prove they detected and responded to security incidents appropriately
- Miss critical audit trails needed during compliance reviews
- Fail to demonstrate due diligence in protecting sensitive data
Also read: Why Your IDS/IPS Isn’t Stopping Breaches (and What to Do About It)
————————————————————————————————————————————————————————————————————————
Case Study: How Ashar Schools Achieved 99.99% Uptime With Proactive Monitoring
Ashar Schools, an educational institution serving hundreds of students, faced recurring network issues that disrupted learning and administrative operations. Their legacy monitoring system provided basic uptime checks but failed to prevent:
- Weekly network outagesduring peak classroom hours
- Slow application performancethat frustrated teachers and students
- Security concerns about unauthorized access to student data
Protected Harbor’s Solution:
- Implemented 24/7 Network Monitoring: Deployed advanced monitoring tools that tracked not just uptime, but performance metrics, security anomalies, and capacity trends.
- Proactive Alerting: Configured alerts to trigger at the first sign of potential issues, rather than waiting for full failures.
- Regular Assessments: Established quarterly network reviews to identify and address emerging risks before they affected users.
Results:
✅ 99.99% uptime achieved within first 90 days
✅ Zero unplanned outages for 18 months and counting
✅ 40% reduction in IT support tickets related to network issues
✅ 100% compliance with educational data protection standards
“Protected Harbor didn’t just give us better monitoring tools – they gave us peace of mind. Now we know about potential issues before they affect our classrooms.” – Ashar Schools IT Director
————————————————————————————————————————————————————————————————————————
Warning Signs Your Network Monitoring Is Failing You
If you’re experiencing any of these issues, your current network security monitoring approach may be putting your business at risk:
- Your Users Report Issues Before Your Tools Do
If employees are consistently noticing problems before your monitoring system generates alerts, you have a visibility gap. - You Can’t Predict Future Capacity Needs
Effective monitoring should help you anticipate when you’ll need more bandwidth, storage, or computing power – not just tell you when you’ve run out. - Security Investigations Take Days Instead of Hours
Without comprehensive logging and easy-to-use analysis tools, identifying the root cause of security incidents becomes a manual, time-consuming process. - You Have “Mystery” Performance Issues
Intermittent slowdowns that disappear before you can diagnose them are often signs of inadequate monitoring. - Compliance Audits Are Stressful Ordeals
If gathering evidence for audits requires manual effort and last-minute scrambling, your monitoring isn’t serving its compliance function.
————————————————————————————————————————————————————————————————————————
What World-Class Network Monitoring Really Looks Like
Protected Harbor has built mission-critical IT infrastructure monitoring systems for hospitals, financial institutions, and SaaS companies with zero tolerance for downtime.
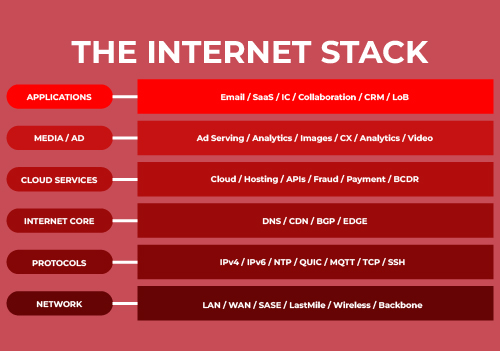
True enterprise-grade monitoring includes:
1. Comprehensive Visibility
- Full-stack monitoring that covers networks, servers, applications, and security events
- Cloud and on-premises coverage with equal depth and detail
- Real-time and historical analysis to identify both immediate issues and long-term trends
2. Intelligent Alerting
- AI-powered anomaly detection that identifies unusual patterns human operators might miss
- Risk-based prioritization that ensures critical issues get immediate attention
- Automated escalation that routes alerts to the right team members based on severity and type
3. Business Context
- Service-aware monitoring that understands how technical issues impact business operations
- Cost-to-resolution forecasting that helps prioritize issues based on financial impact
- Compliance mapping that automatically links monitoring capabilities to regulatory requirements
4. Proactive Optimization
- Capacity forecasting to predict resource needs weeks or months in advance
- Performance baselining to identify gradual degradation before users notice
- Automated remediation that fixes common issues without human intervention
““World-class monitoring isn’t about watching more metrics – it’s about watching the right metrics and knowing what to do when they deviate from normal.”
—Protected Harbor
————————————————————————————————————————————————————————————————————————
Beyond Technology: The Human Guardrails of Effective Monitoring
Even the most sophisticated network monitoring solutions are only as good as the people and processes behind them. At Protected Harbor, we’ve learned that true protection comes from blending cutting-edge technology with human expertise and clear operational discipline.
Our approach centers on three pillars:
1. Expert Eyes, 24/7
Our 24/7 Network Operations Center isn’t just a room with screens -it’s staffed by certified engineers who live and breathe network behavior. These aren’t generic technicians; they’re specialized analysts dedicated to security, performance, and capacity monitoring. But expertise isn’t static. We continuously train our team on emerging threats and technologies because what worked yesterday won’t necessarily work tomorrow.
2. Process Without Paperwork
We’ve replaced chaotic incident response with clear, standardized playbooks for common scenarios. When an alert triggers, your team won’t waste precious minutes figuring out who to call – escalation paths automatically route issues to the right experts within minutes, not hours. And every incident makes us smarter: we systematically incorporate lessons learned into improved processes.
3. Business-Aligned Insights
We translate technical metrics into business impact. Instead of overwhelming you with jargon-filled dashboards like PCI DSS network requirements, we provide executive-level reporting that answers one question: “How does this affect our operations?” Regular review sessions connect monitoring data to strategic decisions, while transparent pricing ensures no surprise costs. After all, effective monitoring shouldn’t be a financial mystery.
This human-powered approach transforms monitoring from a technical necessity into a strategic advantage – ensuring your network doesn’t just remain operational, but actually supports your business goals.
————————————————————————————————————————————————————————————————————————
Don’t Wait for Your Next Network Crisis
If your users report problems before your tools do, or if compliance audits leave you scrambling for logs, your monitoring has already failed you. The next outage, breach, or audit fine is not a question of if — it’s when.
That’s why Protected Harbor specializes in transforming reactive monitoring into enterprise-grade network resilience. With 24/7 engineers, AI-driven anomaly detection, and business-aligned insights, we close gaps before they cost you.
✅ 99.99% uptime delivered
✅ 40% reduction in IT tickets
✅ Zero audit findings across HIPAA, PCI-DSS, and SOC 2 environments
————————————————————————————————————————————————————————————————————————
Get Your Free Network Monitoring Assessment
Stop guessing about your network’s health. Let us provide a clear, actionable assessment of your current monitoring capabilities and identify gaps that could be putting your business at risk.
Your Free Assessment Includes:
✅ Comprehensive visibility audit of your environment
✅ Security gap analysis to expose blind spots
✅ Compliance readiness review (HIPAA, PCI, SOC 2)
✅ Customized roadmap to bulletproof your network
Stop guessing. Start protecting. Request your assessment today.






 The Role of IT in Business Continuity
The Role of IT in Business Continuity

 3. Steps to Achieve and Maintain Compliance
3. Steps to Achieve and Maintain Compliance

 6. Supporting Remote and Hybrid Workforces
6. Supporting Remote and Hybrid Workforces

 7. Software Management
7. Software Management

 Best Practices for Proactive IT Monitoring
Best Practices for Proactive IT Monitoring

 Step 5: Contact Your Internet Service Provider (ISP)
Step 5: Contact Your Internet Service Provider (ISP)




 5. Adjusting System Settings
5. Adjusting System Settings