MSP Trends 2025

MSP Trends 2025
Unparalleled challenges and opportunities await MSPs in the rapidly evolving tech landscape. Leveraging state-of-the-art technologies like AI and aligning strategies with emerging industry trends will be crucial for success as we approach 2025. This blog explores the top MSP Trends 2025 and how AI is transforming MSP operations and highlights critical predictions for the future of the industry.
AI-Powered Transformation in MSPs
Artificial intelligence is reshaping MSP operations, driving efficiency, enhancing customer service, and strengthening cybersecurity. Here are the key areas where AI is making a significant impact:
-
Cybersecurity: Precise Combat Against Threats
MSPs use AI to monitor and neutralize cyber threats proactively. From endpoint monitoring to automating vulnerability assessments, AI enhances security measures, ensuring compliance and protecting client data. However, as AI is utilized by both defenders and attackers, continuous innovation is vital.
-
Customer Support: Elevating Experiences
AI-powered chatbots and intelligent knowledge bases are revolutionizing customer service. MSPs can respond to inquiries in real-time, automate ticketing, and generate tailored instructions and scripts, reducing costs while maintaining quality service.
-
Engineering: Automating Repetitive Tasks
From creating PowerShell scripts to automating system configurations, AI empowers engineers to focus on innovative, high-value projects. This increases efficiency and reduces human errors in complex tasks.
-
Marketing and Communications
MSPs are adopting AI tools to craft effective marketing campaigns. These tools enable businesses to create optimized content, personalize customer interactions, and enhance SEO efforts, making marketing faster and more impactful.
-
Training and Development
AI fosters engaging training experiences for staff and clients. Tools that create guides, generate subtitles, and simulate real-world scenarios ensure MSP teams are better prepared to tackle challenges.
 Key Predictions for MSP Trends in 2025
Key Predictions for MSP Trends in 2025
To thrive in a dynamic and competitive landscape, MSPs must adapt to the following pivotal trends shaping the future of the industry:
1. The Rise of AI-Driven Automation
AI is no longer a luxury but a cornerstone of MSP operations. Automation powered by AI is streamlining tasks like predictive maintenance, patch management, and vulnerability assessments. Tools such as AI-driven chatbots and automated ticket systems significantly enhance customer support by addressing concerns swiftly and accurately. Cyber defense has also seen a revolutionary shift, with AI actively monitoring for suspicious behavior and neutralizing threats in real-time. By adopting AI-driven automation, MSPs can reduce operational costs, improve efficiency, and deliver superior client outcomes.
2. Zero Trust as the Security Standard
The Zero Trust model is gaining traction as the new benchmark for network security. Unlike traditional perimeter-based security models, Zero Trust operates on the principle of “never trust, always verify.” This approach requires continuous authentication and strict access controls, making it ideal for combating modern cyber threats. For MSPs, integrating Zero Trust principles into their service offerings ensures robust security solutions that meet clients’ growing needs for data protection and regulatory compliance.
3. Multi-Cloud Mastery
With businesses increasingly relying on multiple cloud platforms, managing multi-cloud environments is becoming a critical capability for MSPs. A multi-cloud strategy allows organizations to optimize costs, enhance performance, and avoid vendor lock-in. By offering expertise in this area, MSPs can help clients navigate the complexities of cloud integration, workload distribution, and data migration, making themselves indispensable partners in a cloud-first world.
4. IoT Management as a Priority
The rise of Internet of Things (IoT) devices presents both opportunities and challenges for MSPs. While IoT technology can improve operational efficiency and enable innovative applications, it also expands the attack surface for cyber threats. MSPs must implement robust security protocols to protect connected devices, monitor network activity for anomalies, and respond swiftly to potential breaches. By prioritizing IoT management, MSPs can offer comprehensive solutions that address this growing area of concern.
5. Embracing XaaS (Everything as a Service)
The “Everything as a Service” (XaaS) model is reshaping how businesses consume technology. From data storage and cybersecurity to consulting services, XaaS provides flexibility, scalability, and cost-efficiency. For MSPs, transitioning to a subscription-based service model allows them to meet the evolving demands of clients while generating predictable revenue streams. Adopting XaaS positions MSPs as adaptable and forward-thinking providers in an increasingly subscription-driven economy.
6. Predictive Analytics Growth
Predictive analytics is emerging as a game-changer for decision-making across industries. By analyzing historical and real-time data, MSPs can forecast trends, identify risks, and recommend proactive measures. This capability enables MSPs to offer unparalleled insights that drive business success. However, securing the data used in AI-driven analytics is crucial to ensuring accuracy and reliability. By combining advanced analytics with robust cybersecurity, MSPs can unlock the full potential of data-driven strategies.
7. Focus on Energy Efficiency
As data centers grow more energy-intensive, optimizing energy consumption is becoming a top priority. Clients are increasingly seeking solutions that align with sustainability goals while reducing operational costs. MSPs can seize this opportunity by offering energy-efficient services such as workload optimization, infrastructure consulting, and recommendations for green practices. By demonstrating a commitment to environmental responsibility, MSPs can attract eco-conscious clients and differentiate themselves in the marketplace.
Conclusion
The MSP industry is poised for transformative growth, driven by advancements in AI, evolving security standards, and changing client expectations. Embracing these trends is not just about staying relevant but about setting the stage for long-term success. By adopting AI-driven automation, mastering multi-cloud environments, and addressing emerging challenges like IoT security and energy efficiency, MSPs can position themselves as indispensable partners in their clients’ digital transformation journeys.
At Protected Harbor, we are at the forefront of this evolution. Our proactive, client-focused approach leverages the latest technologies to deliver unparalleled reliability, security, and scalability. Whether you’re looking to enhance operational efficiency, secure your IT environment, or embrace cutting-edge innovations, we’re here to guide you every step of the way.
Future-proof your business today! Contact Protected Harbor to learn how we can empower your MSP operations with industry-leading solutions. Let’s redefine managed services together.


 Best Practices for Network Infrastructure Design
Best Practices for Network Infrastructure Design

 4. iOS 18’s Simplified Privacy and Security Settings
4. iOS 18’s Simplified Privacy and Security Settings
 How to Prepare for a Cybersecurity Audit
How to Prepare for a Cybersecurity Audit


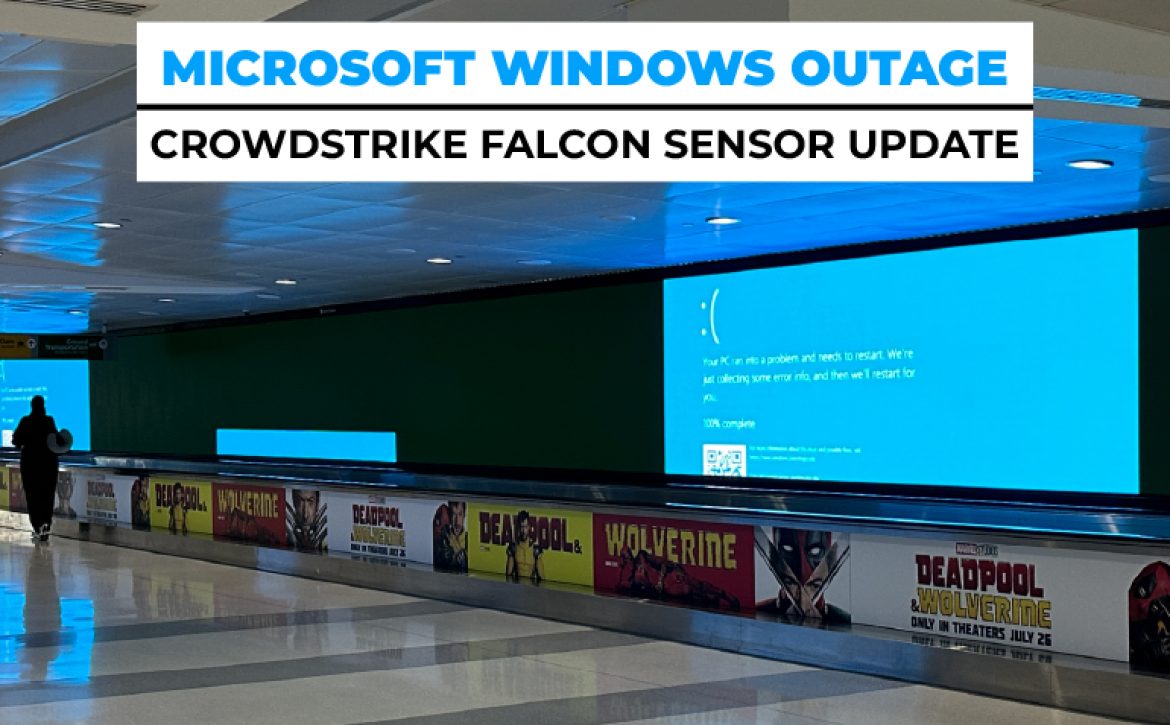
 Investigation and Expert Opinions
Investigation and Expert Opinions


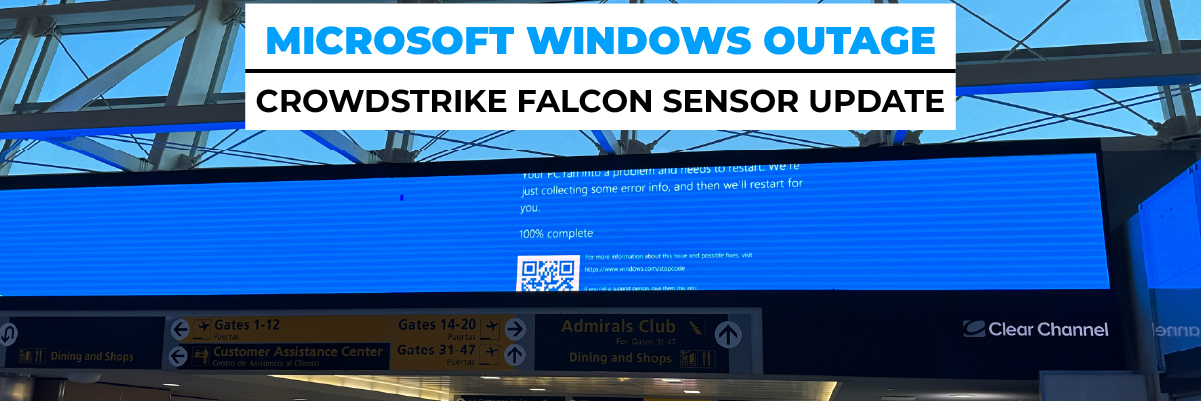

 4. Disaster Recovery and Business Continuity
4. Disaster Recovery and Business Continuity