Ransomware Risk Isn’t Random — It’s Designed by Your Environment
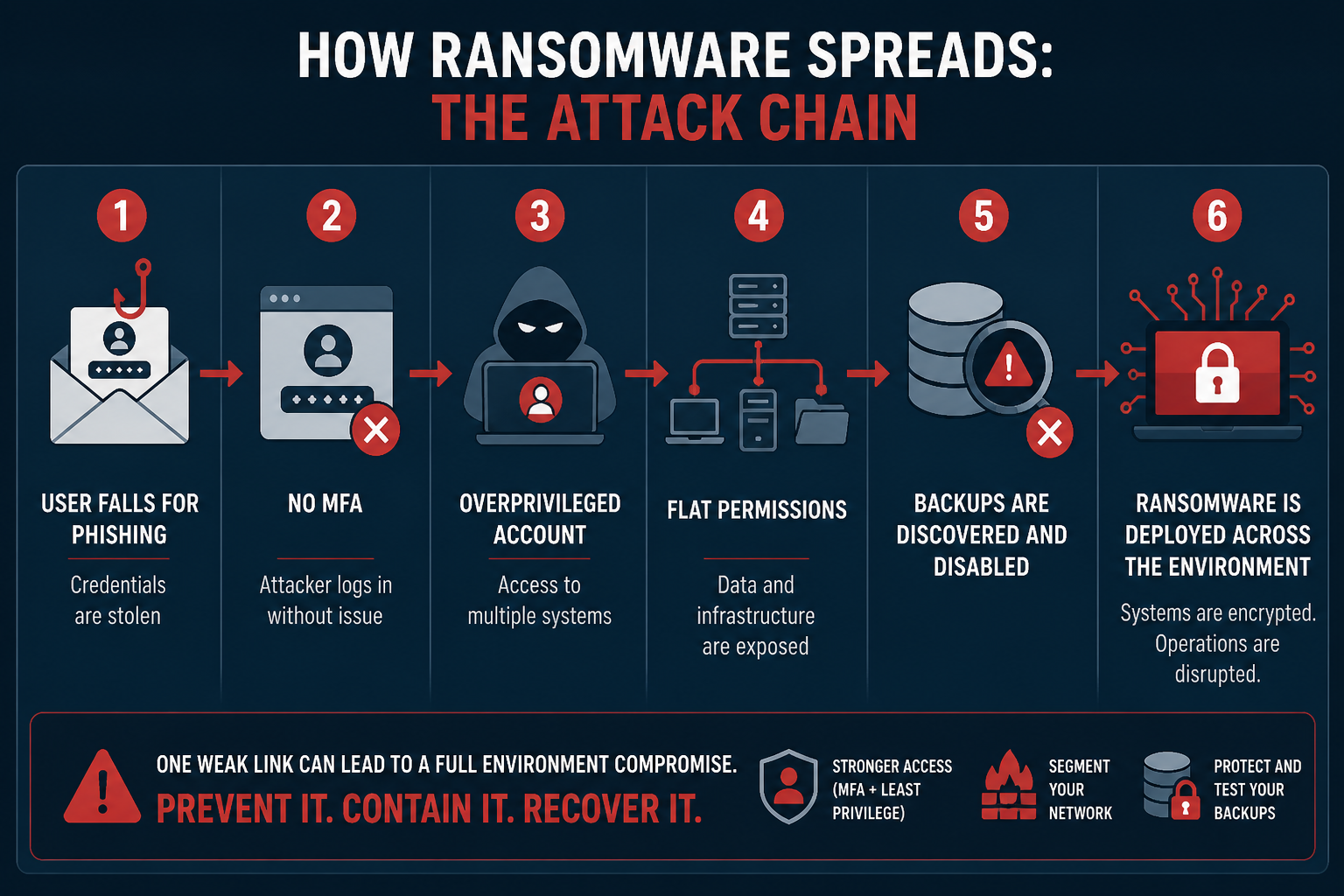
Most cyberattacks don’t need to rely on advanced exploits. Many successful incidents rely on exploiting predictable, preventable internal weaknesses. Attackers don’t need to outsmart your defenses — they can just look for:
- Weak or missing authentication controls
- Excessive access once inside
- The ability to destroy recovery options
These are not edge cases — they’re common operational gaps. Ransomware success isn’t about how advanced the attacker is — it’s about how exposed your environment is. Ransomware doesn’t succeed because an attacker got lucky. It succeeds because the environment allowed it to succeed. Ransomware follows the path you’ve already built. Attackers don’t need to create complexity when they can just exploit what’s already there.
In our previous blogs, we looked at how mixed-use servers and flat networks increase your vulnerability to ransomware. In this blog, we are going to focus on common identity/ access weaknesses, and why protecting your backups is one of the most crucial ways to save your business.
The Keys to the Kingdom
Organizations must properly manage user accounts and be mindful of excessive permissions. If one account can access everything, one compromise can destroy everything. Mismanaged accounts and permissions can look like:
- Users with access far beyond their job function
- Service accounts with domain-level privileges
- Shared admin credentials across teams
- Wide-open file shares
- Dormant accounts still active
Many environments evolve over time without governance, which can lead to permission creep, forgotten accounts, and inconsistent access policies. These issues also occur when an organization is coordinating multiple vendors and there is no clear ownership. Once an attacker gains any valid credentials, they can blend in as a legitimate user, avoid detection by security tools, and move faster than traditional defenses can react.
If an attacker obtains access to an ‘overprivileged’ account, you’re essentially giving them the keys to the kingdom. This broad access means attackers don’t need to hack your systems to wreak havoc — all they need to do is log in.
Once in, attackers will:
- Use stolen credentials to access multiple systems
- Escalate privileges using misconfigurations
- Move laterally without triggering alarms
- Quickly access sensitive data and critical systems
Authentication = trust. If identity controls are weak, attackers can inherit that trust.
Hidden Risks & How to Prevent Them
Hidden risks include:
- Dormant accounts: Old employees, contractors, test accounts.
- Shadow IT: Accounts created outside of IT oversight.
- Lack of access reviews: Permissions are never reevaluated.
- Flat directory structures: No separation of privilege tiers.
- Wide-open share permissions: “Everyone” or “Domain Users” can access critical shares.
All of these risk factors create an easy staging ground for ransomware encryption.
What to do instead:
- Enforce least privilege (only what’s needed, nothing more)
- Conduct regular access reviews
- Automate processes for employees who join, move, or leave
- Segment administrative roles
- Lock down shared resources with clear ownership
Ransomware Doesn’t Need to Break In — It Logs In & Spreads
Let’s see an example. An organization tends to be lax with their permissions, but their security is otherwise strong. A user unknowingly clicks on a malicious link, introducing malware into the environment. Once inside the environment, the attackers focus on getting access to local admin so they can extend that access to the entire deployment. This is known as escalation of privilege. If the organization does not utilize deep monitoring, they might not be alerted to suspicious activity in their environment. By the time they realize, it may already be too late. Once an organization is locked out of their deployment, an attacker may deploy ransomware or scan the deployment for sensitive information (e.g., social security numbers, payment information, files that contain keywords like ‘password’ in the name).
Attackers always target data because data is currency. Once your data is within their grasp, they can steal it, sell it, hold it for ransom — your entire organization will be jeopardized.