From Incidents to Outages: The Cost of Getting It Wrong
One of the hardest parts for an attacker is actually getting into your system:
Crafting an email that looks legitimate to trick someone into clicking a malicious download link.
Finding their way into exposed remote desktop access.
Exploiting a public Wi-Fi network.
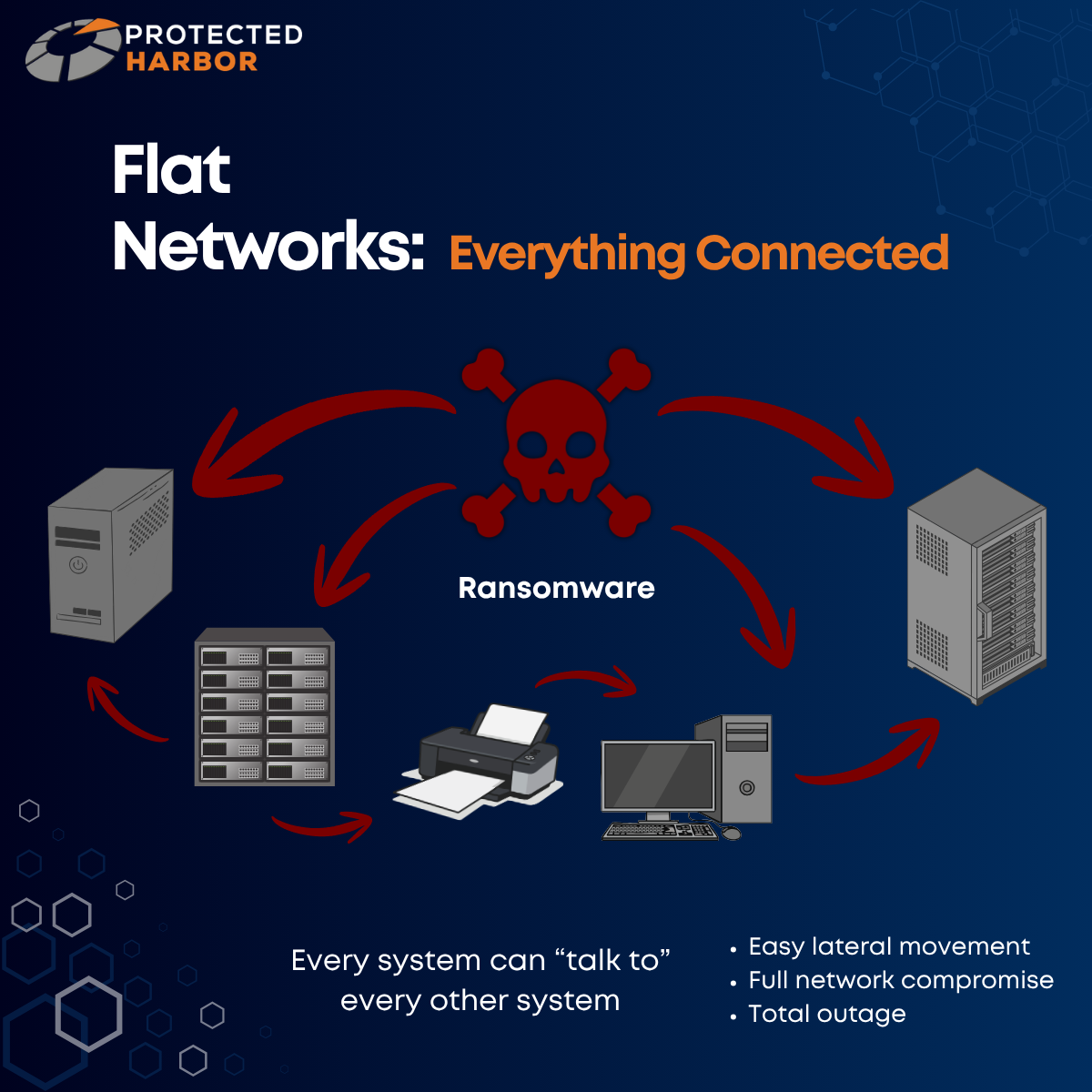
But once they’re in? It’s go time. When a single compromised machine can take down your entire organization, the real issue isn’t how the attacker got in — it’s how far they were allowed to go once they did. During an attack, minutes and hours matter more than almost anything else. Slowing the spread of malware increases your chances of early detection, isolating key systems, and preventing the full deployment from being impacted.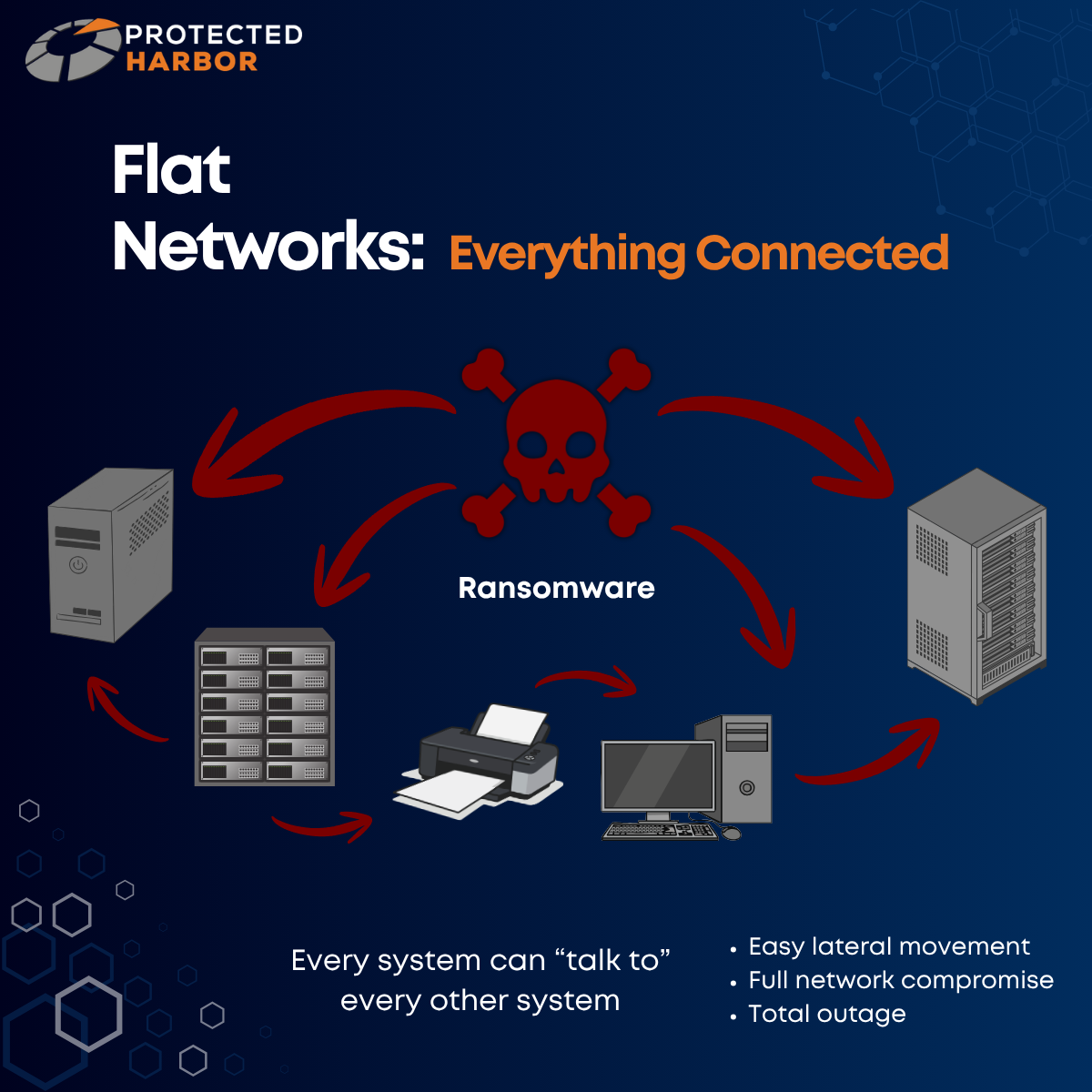
If a fire breaks out in a dense forest, the entire forest will burn quickly and uncontrollably. If an attacker gains access to a network with little to no segmentation, there is no barrier to movement. The consequence?
Ransomware will spread in minutes, not hours.
Not only can the ransomware spread quicker, but it’s easier for attackers to access high-value systems like your file servers, backups, and domain controllers. The issue here is lateral movement. The initial breach is often small, but the damage becomes massive due to internal spread. In this context, segmentation would be firebreaks (strips of land where trees and vegetation are removed in order to stop or slow the spread of a fire). They won’t prevent fires from starting, but they contain the damage.
Why Segmentation Failures Lead to Total Outages
When ransomware hits a flat network, your entire environment will be encrypted simultaneously and you’ll have a full outage on your hands within hours. This means a full operational shutdown, longer recovery timelines, and a higher pressure to pay the ransom.
When an attacker breaches a flat network, they don’t need to break in again. They can freely move from:
- User device to application server
- Application server to database
- Database to backups
- Backups to domain control
Your infrastructure is allowing unrestricted traversal across systems that were never meant to be exposed to each other.
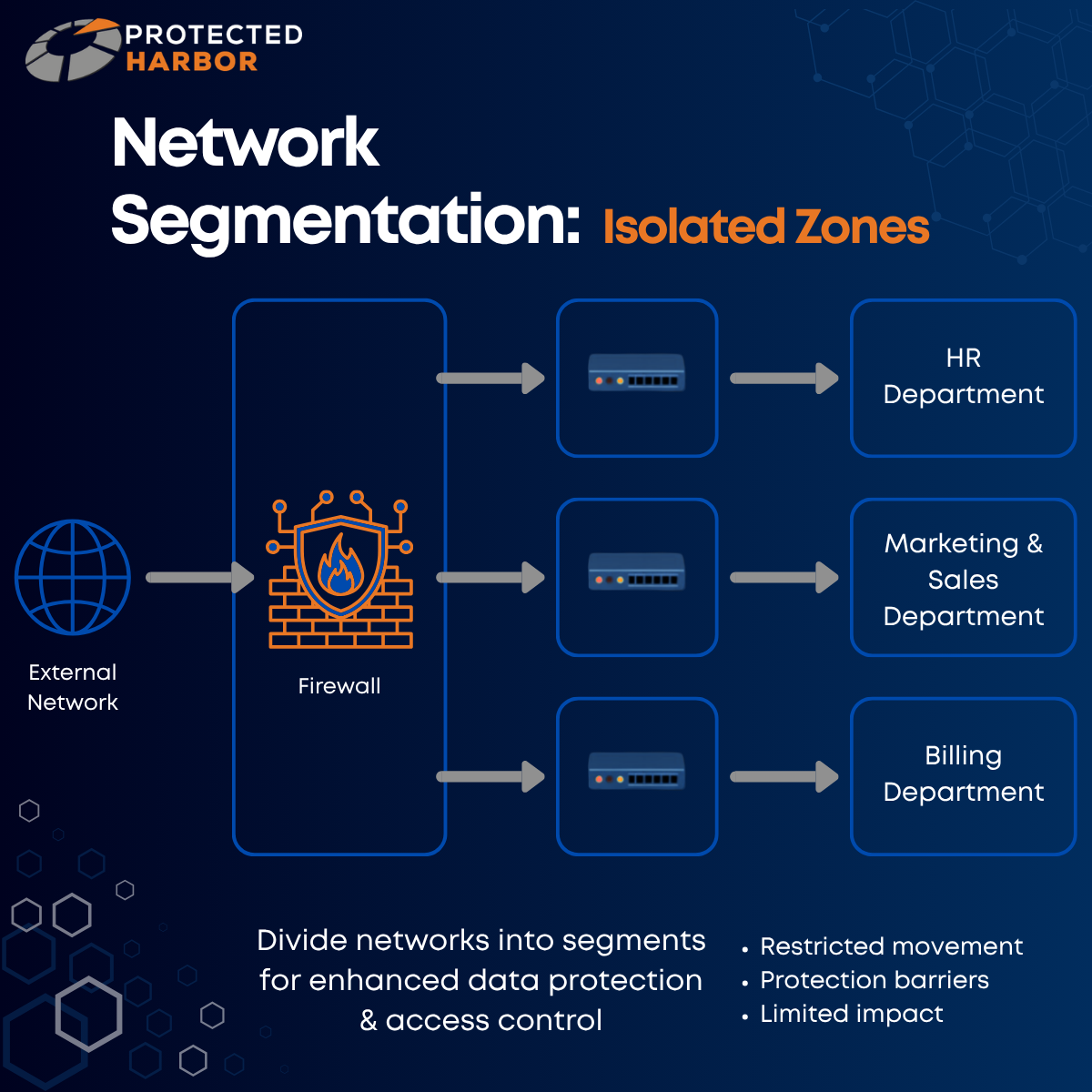
Segmentation often determines whether a ransomware attack means one department is down, or the entire company goes offline. Every minute of downtime caused by an attack hurts your organization.
Frustrated customers.
Idle staff.
Missed transactions.
Lost revenue.
Reputational damage.
Increased risk of lawsuits and fines.
When one system goes down? That’s manageable.
When everything goes down? The fate of your entire organization is on the line.
The worse the spread, the longer you’ll be offline. The longer your operations are shut down or you’re without access to your data, the higher the chances are that you’ll never recover. Organizations experiencing data loss for more than 10 days face a 93% bankruptcy rate within a year of a cyberattack. Ransomware can cripple your business if you’re not actively taking steps to ensure you’re protected. Segmentation slows attacks down, limits the blast radius, and buys time for detection and response. In the aftermath, it also makes recovery faster, more contained, and less costly.
How Do Flat Networks Occur?
Flat networks are the result of:
- Organic growth without architectural oversight
- Multiple vendors with no single point of accountability
- “Get it working” decisions that are never revisited
- A lack of understanding of application behavior
No one designs bad infrastructure on purpose, but flat networks aren’t accidental. Segmentation is an architectural decision. It doesn’t require specialized hardware, you just need to be thinking about it. Flat networks happen when infrastructure is built generically, often due to a lack of expertise. Many organizations end up with a flat network simply because they, or their IT team, don’t know any better.
Segmentation is how you define the boundaries of your application. Common segmentation mistakes include:
- Overly permissive firewall rules
- Backup systems on the same network as production
- Not restricting admin pathways
- Shared credentials between systems
- Leaving default accounts enabled
- Allowing users to install and manage software
As attackers continue to develop new and increasingly advanced methods, this has led to Zero Trust becoming a focus in the industry when it comes to security principles. Zero Trust operates on the idea that you never blindly trust anything in an environment. You must always authenticate and verify every single action and/or change. Zero Trust means that IT teams can no longer operate on implicit trust — they must operate on explicit trust.