Eye Care Leaders Data Breach Caused by Cloud EHR Vendor. Don’t be the Next.
Eye Care Leaders Data Breach Caused by Cloud EHR Vendor. Don’t be the Next.
 The databases and system configuration files for Eye Care Leaders, a manufacturer of cloud-based electronic health record and practice management systems for eye care practitioners, were recently hacked.
The databases and system configuration files for Eye Care Leaders, a manufacturer of cloud-based electronic health record and practice management systems for eye care practitioners, were recently hacked.
What Happened
The breach reportedly compromised the organizations’ cloud-based myCare solution, with hackers obtaining access to the electronic medical record, patient information, and public health information (PHI) databases on or around December 4, 2021, according to breach notification letters provided by some of the affected practices. The hacker then erased the databases and system configuration files.
When the breach was discovered, the company promptly locked its networks and initiated an investigation to avoid additional unauthorized access. That investigation is still underway, and it’s unclear how much patient data was exposed. However, it’s possible that sensitive data was seen and exfiltrated before the database was deleted. Patients’ names, dates of birth, medical record numbers, health insurance information, Social Security numbers, and personal health information regarding care received at eye care offices were all stored in the databases.
More than 9,000 ophthalmologists use the Durham, NC-based company’s products. It’s unclear how many providers have been affected at this time. Summit Eye Associates, situated in Hermitage, Tennessee, has revealed that it was hacked and that the protected health information of 53,818 patients was potentially stolen. Evergreen Health, a Kings County Public Hospital District No. 2 division, has also acknowledged that patient data has been compromised. According to reports, the breach affected 20,533 people who got eye care at Evergreen Health. The breach has been confirmed by Allied Eye Physicians & Surgeons in Ohio, which has revealed that the data of 20,651 people was exposed.
The records of 194,035 people were exposed due to the breach at Regional Eye Associates, Inc. and Surgical Eye Center of Morgantown in West Virginia. Central Vermont Eye Care (30,000 people) recently reported a data breach affecting EHRs. However, HIPAA Journal has not been able to establish whether the cyberattack caused the data loss at Central Vermont Eye Care on Eye Care Leaders.
Confidential Information Exposed
In this distressing incident, Eyecare Leaders, a prominent eye care technology company, experienced a severe data breach, compromising the sensitive patient information of numerous Retina Consultants of Carolina patients. The breach has raised significant concerns about the security and privacy of patients’ medical records and personal data.
Eyecare Leaders, known for providing comprehensive technology solutions to eyecare practices, play a crucial role in managing and safeguarding sensitive information within the healthcare industry. However, this breach has exposed vulnerabilities within their systems, potentially leading to unauthorized access and misuse of patient data.
The breach, possibly a ransomware attack, highlights the pressing need for robust cybersecurity measures in the healthcare sector, urging organizations like Eyecare Leaders to strengthen their data protection protocols and mitigate the risk of future breaches. Meanwhile, Retina Consultants of Carolina patients are advised to monitor their accounts, remain vigilant against potential identity theft, and seek guidance from healthcare providers to ensure the security of their confidential information.
Update
Over the last two weeks, the number of eye care providers affected by the hack has increased. The following is a list of eye care practitioners who have been identified as being affected:
| Affected Eye Care Provider | Breached Records |
| Regional Eye Associates, Inc. & Surgical Eye Center of Morgantown in West Virginia | 194,035 |
| Shoreline Eye Group in Connecticut | 57,047 |
| Summit Eye Associates in Tennessee | 53,818 |
| Finkelstein Eye Associates in Illinois | 48,587 |
| Moyes Eye Center, PC in Missouri | 38,000 |
| Frank Eye Center in Kansas | 26,333 |
| Allied Eye Physicians & Surgeons in Ohio | 20,651 |
| EvergreenHealth in Washington | 20,533 |
| Sylvester Eye Care in Oklahoma | 19,377 |
| Arkfeld, Parson, and Goldstein, dba Ilumin in Nebraska | 14,984 |
| Associated Ophthalmologists of Kansas City, P.C. in Missouri | 13,461 |
| Northern Eye Care Associates in Michigan | 8,000 |
| Ad Astra Eye in Arkansas | 3,684 |
| Fishman Vision in California | 2,646 |
| Burman & Zuckerbrod Ophthalmology Associates, P.C. in Michigan | 1,337 |
| Total | 522,493 |
 Protected Harbor’s Take On The Matter
Protected Harbor’s Take On The Matter
There are more than 1,300 eye care practices in the United States alone. And with more than 24 million Americans affected by some form of visual impairment, the demand for eye care services continues to grow. In response to these growing needs, we have seen an increase in cloud-based electronic health record management software solutions to streamline operations while increasing efficiency and security.
Unfortunately, this also means that cybercriminals see the eye care industry as a prime target for hackers because their information is so sensitive and accessible. That’s why you must know which cloud EHR vendors were hacked recently.
Protected Harbor’s 5 ways to prevent unauthorized access to your company data:
- Strong Password Policy– Having your users add symbols, numbers, and a combination of characters to their passwords makes them more difficult to crack. Having a minimal amount of characters and changing it periodically (every 60 or 90 days) ensures that outdated passwords aren’t reused for years, making it much easier to get unwanted access to the account.
- MFA– Multi-factor authentication is a great approach to ensure you only access the account. You will need another device (usually your mobile device) nearby in addition to your usual login and password since you will be required to enter a code that will be produced instantly.
- Proactive Monitoring- Preventing unauthorized access is the initial step, but monitoring login attempts and user behaviors can also provide insight into how to prevent it best. For example, if you have logs of failed login attempts for a single user. You can launch an inquiry to see whether the user merely forgot their password or if someone is attempting to breach the account.
- IP Whitelisting- IP Whitelisting compares the user’s IP address to a list of “allowed” IP addresses to determine whether or not this device is authorized to access the account. If your firm only uses one or a limited number of IP addresses to access the internet, as is usually the case, you can add a list of IP addresses that are granted access. All other IPs will be sent to a page that isn’t allowed.
- SSO (Single Sign-On)- If your firm has a centralized user directory, using it to acquire access makes things more accessible and more manageable for you. You’ll have to remember one password, and if something goes wrong, your network administrator can deactivate all of your applications at once.
Richard Luna, CEO of Protected Harbor, stated: Unfortunately, this is how things will be in the future. The development tools used to create websites and mobile applications were created in the 1990s. Data transferability, or the ability to move data from one device to another, was a critical concern back then. The emphasis back then was on data proliferation. FTP comes to mind as a secure method with no encryption. Authentication was designed for discerning between good actors, not to harden data and protect against data theft because all data exchanges were between good actors back then. Now that we live in a different environment, we may expect more data breaches unless security is built into data transfer protocols rather than bolted on as an afterthought.
We’ve been helping businesses respond to these attacks for some time, including ransomware attacks and cross-pollinating destructive IP attacks across numerous access points and multiple AI use. If a company has 50 public IPs and we’re proactive monitoring the services behind them, and a bad actor assaults one of them, ban them from all entry points in all systems, even if it involves writing a synchronized cron job across firewalls or other protection devices. Add in artificial intelligence (AI) and comprehensive application monitoring, and a corporation has the tools to detect and respond to such threats quickly.
Final Thoughts
Data security isn’t a one-time or linear process. You must invest in software vendors, ongoing resources, time, and effort to ensure data security against unwanted access.
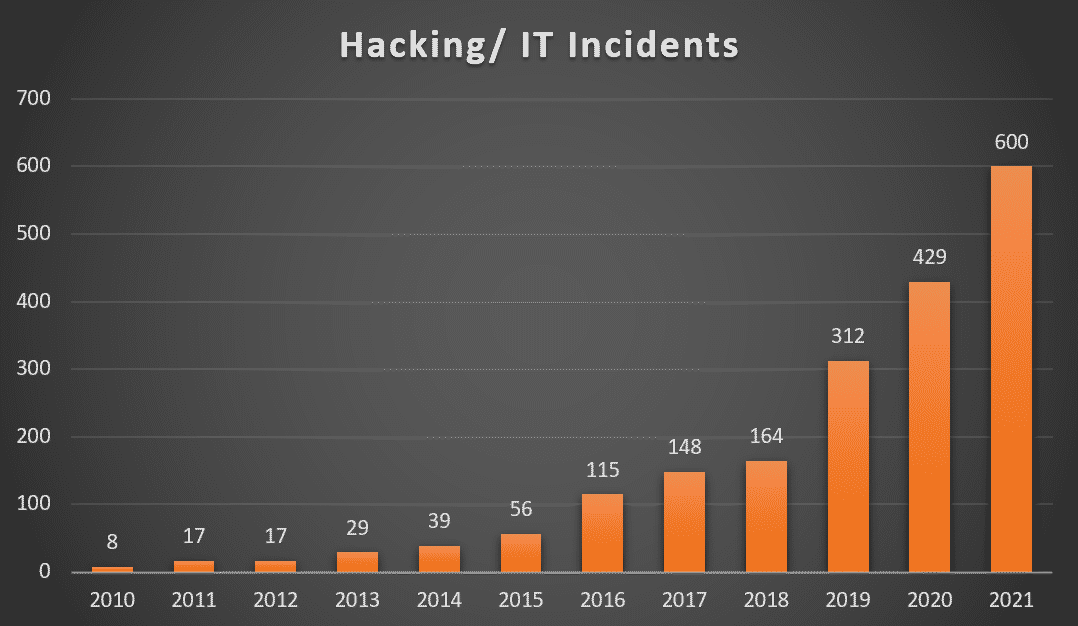
Cybercriminals are becoming more sophisticated every day, and they are employing cutting-edge technologies to target businesses and get illicit data access.
As the number of data breaches rises, you must become more attentive. It’s critical that your company implements concrete security measures and that each employee prioritizes cybersecurity.
If you’d want us to conduct an IT security audit on your current security policies, we’ll work with you to ensure that you’re well-protected against unauthorized data access and other cyber risks. Contact us today!




 Data security has become a point for convergence with the widespread use of the Internet and the adoption of network applications. The information and data transmitted over the Internet should ensure its integrity, confidentiality, and authenticity. One of the most effective ways to resolve this issue is to leverage advanced encryption techniques. Encryption is one of the most crucial methods to secure data online. It’s a process of converting plain text into ciphertext that is not understood or transformed by unauthorized users. Encryption is a cybersecurity measure protecting sensitive data using unique codes that encrypt data and make it unreadable to intruders. This article will discuss fast-speed symmetric encryption, secure asymmetric encryption, and hash functions. Then we’ll figure out the importance of encryption and how can end-to-end data encryption prohibit data breaches and security attacks.
Data security has become a point for convergence with the widespread use of the Internet and the adoption of network applications. The information and data transmitted over the Internet should ensure its integrity, confidentiality, and authenticity. One of the most effective ways to resolve this issue is to leverage advanced encryption techniques. Encryption is one of the most crucial methods to secure data online. It’s a process of converting plain text into ciphertext that is not understood or transformed by unauthorized users. Encryption is a cybersecurity measure protecting sensitive data using unique codes that encrypt data and make it unreadable to intruders. This article will discuss fast-speed symmetric encryption, secure asymmetric encryption, and hash functions. Then we’ll figure out the importance of encryption and how can end-to-end data encryption prohibit data breaches and security attacks. Hash Functions
Hash Functions
 A host of advanced and evolving
A host of advanced and evolving 

 Wellstar Health System announced on Friday afternoon that its email system had been hacked.
Wellstar Health System announced on Friday afternoon that its email system had been hacked. Use Encryption
Use Encryption

 Technological advancement in the current digital era has increased vulnerabilities in businesses using Microsoft products. It has affected most
Technological advancement in the current digital era has increased vulnerabilities in businesses using Microsoft products. It has affected most  Microsoft MSHTML
Microsoft MSHTML

 Patient Data Theft: High risk
Patient Data Theft: High risk