What is the most common cause of healthcare data breaches?
Patient’s medical records are a goldmine for malicious hackers—if they can get their hands on them. According to Cisco Internet Security Threat Report, healthcare is currently the most targeted industry by cybercriminals.
Health data breaches have been on the headlines for a while now. From the crippling breach of Anthem to the compromising of 10 million patient records at UCLA Health — nothing is sacred when it comes to cyberattacks these days. While the impact of security incidents might differ depending on their magnitude, it seems that poorly protected IT systems and hacking/IT incidents are often the biggest culprits in causing privacy and financial setbacks.
Healthcare data breaches are on the rise. Although many are concerned with hacking, several factors could potentially cause a significant healthcare data breach.
Common causes of healthcare data breaches!
Data breaches are becoming more and more common. With the rise of hacking, phishing, malware attacks, and new security regulations, all healthcare organizations need to stay proactive in protecting their data.
The most common cause of data breaches for healthcare organizations is malicious or cyber-criminal attacks. Data breaches can come from various sources, including hackers stealing protected health information (PHI) from an organization’s database, unencrypted devices, or a weak, stolen password. One of the biggest causes of healthcare data breaches is misconfigured medical devices and office equipment. Medical device security remains a major concern for organizations. Click here to know how do breaches happen and how to prevent them?
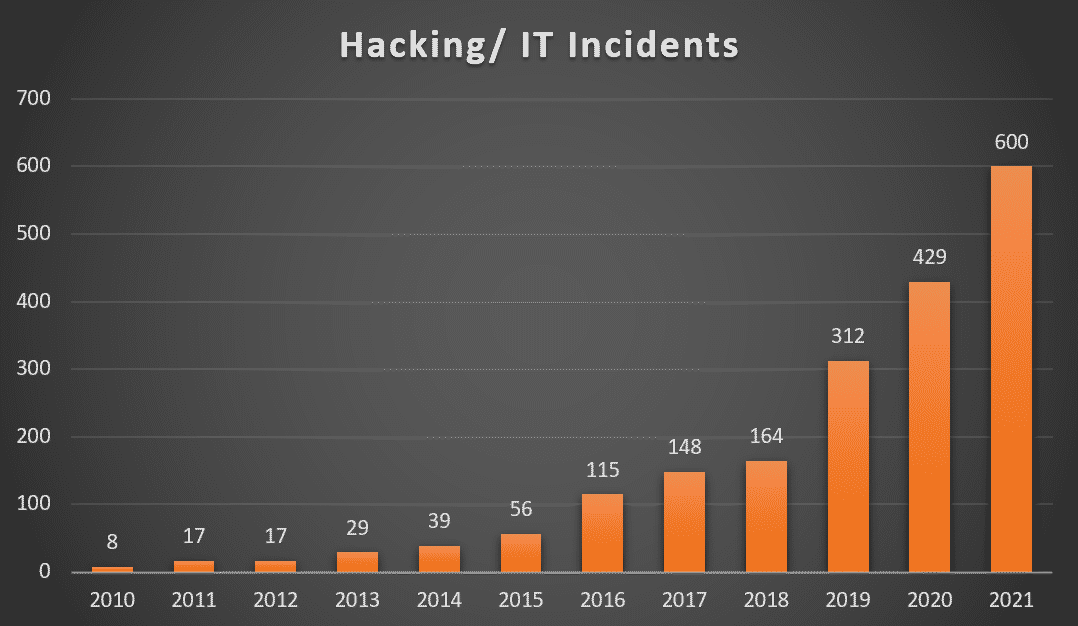
Hacking/ IT Incidents accounts for 47% of healthcare data breaches making it the #1 cause of healthcare data breaches.
(Source: Electronic Health Reporter)
 Patient Data Theft: High risk
Patient Data Theft: High risk
Health care industry members are all too familiar with data theft and new methods of exfiltrating information from connected medical devices such as electronic medical records (EMRs) and protected health information (PHIs). IP-enabled medical devices can be easily exploited by experienced hackers because of minimal access controls and known vulnerabilities. A hacker may then take data directly from the medical device, but since medical devices typically contain limited data, he is more likely to go to servers, data centers, or other devices on the network, like the XP workstation that is connected to the electronic medical record. Data breaches in healthcare are defined as theft and loss 32% of the time, compared to only 15% in different industries, 2nd to Hacking and IT incidents, as per Healthcare drive. With the number of high-profile breaches in healthcare over the past three years, healthcare organizations need tighter controls to mitigate this risk.
What is the cost to your company?
According to IBM’s Cost of Data Breach Report 2021:
- Healthcare organizations spent an average of $161 per breached record in 2021, which is expected to increase in the future.
- On average, it takes 329 days to identify a breach.
The reports show that the cost of data breaches has risen once again, reaching a record high since IBM first published the report 17 years ago. The average cost of a data breach increased by 10% year over year, to $4.24 million per incident and that of healthcare data breaches increased by $2 million to $9.42 million per incident in 2021. The average cost of ransomware attacks was $4.62 million per incident.
How can you avoid a data breach?
- Back up data– Having a proper backup schedule and implementing a secure process to access the off-site data is a preliminary requirement. Confirm that your backup/recovery partner is also HIPAA compliant. Cloud hosting solutions can also be considered for better security.
- Two factor authentication- Multi-factor authentication, also known as 2FA, is a simple concept that can be implemented by companies easily. A key benefit of two-factor verification lies in its very name: it requires two variables to access an account, just as you need two keys to enter a house. The security is therefore twice as strong.
- Safeguard data and devices- Ensure that the tools and policies for security are implemented, securing all the devices accessing your network. Remote monitoring for unauthorized access and unusual activity can opt. Limit and set proper data control and access for the devices.
- Train and educate staff– create a policy for regular security training and practice sessions. Identifying phishing emails, ensuring password complexity, and adhering to anti-malware protocols should be a part of this training. More details
To wrap things up!
Security and compliance are among the top factors healthcare organizations consider when adopting new technologies. Many organizations didn’t or were not able to take the time to strategically align new cloud-based tools and platforms with existing security standards as they transitioned to remote work after the pandemic.
Security and privacy should be a priority when working with technology partners in healthcare. It is a trusted partner’s responsibility to ensure users’ privacy and security, having incorporated a variety of safeguards into their processes, designs, and code, as well as constructing the infrastructure to ensure careful protection of user information. Cisco, Greenway, GE Healthcare, and Protected Harbor are some of the most trusted and reliable healthcare IT solution providers who take pride in their experience of delivering solutions to healthcare and other organizations.






