Inside the IT Graveyard: 5 IT Failures We See Every Week

Inside the IT Graveyard: 5 IT Failures We See Every Week (And How to Escape Them)
Every week, we walk into organizations where the same five failures quietly undermine performance. These failures aren’t rare accidents – they’re predictable, preventable, and costly. Gartner estimates the average cost of IT downtime at $5,600 per minute, and the average cost of a serious compliance failure is now in the tens of millions per incident (IBM/Ponemon). For executives, that translates to valuation hits, compliance scrutiny, stalled initiatives, and frustrated customers.
The good news? These failures can be eliminated. Let’s step inside the IT graveyard and look at the five most common issues we uncover- and, more importantly, how to escape them.
Failure #1: Set-and-Forget Infrastructure
The Problem: Too many organizations treat their core network and server infrastructure like appliances – install them and forget about them. This neglect creates a prime target for cyberattacks like ransomware and data breaches, on top of being a leading cause of unplanned downtime. We see servers running on outdated software, firewalls with obsolete rules, and switches on the verge of failure.
Business Impact: For executives, this isn’t a technical hiccup – it’s a direct hit to the bottom line. Unplanned downtime halts revenue and productivity, while a security incident from an unpatched system leads to millions in recovery costs, regulatory fines, and irreparable brand damage.
The Protected Harbor Difference: We don’t just monitor your systems; we own the stack. Our engineers proactively manage and maintain the infrastructure, applying patches, predicting failures before they happen, and providing free upgrades to keep your technology current. We treat your infrastructure with the same obsessive care we give our own.
“The most expensive words in IT are, ‘I didn’t know it could do that.’ Our job is to ensure you know exactly what your technology is capable of – and, more importantly, what it’s about to fail at – so we can prevent disruption before it costs you.” —Nick Solimando, CTO, Protected Harbor
Failure #2: Compliance Checklist Mentality
The Problem: Many organizations view compliance (like HIPAA, PCI, SOC 2, or GDPR) as a box-ticking exercise – a burdensome audit to pass once a year. However, simply noting a vulnerability to an auditor is not the same as resolving it. Checking a box ≠ security. This creates a fragile environment where security is a façade, and the moment an auditor isn’t looking, vulnerabilities creep in, leaving sensitive data exposed. It’s critical to note that regulatory fines can double or triple if violations are knowingly ignored.
Business Impact: A compliance failure is a business failure. The financial penalties are severe, but the reputational damage from a data breach can be fatal, especially in trust-based industries like Legal and Healthcare.
The average cost of a data breach in the healthcare sector is now over $10.9 million per incident when accounting for fines, legal fees, and brand remediation. (Source: IBM/Ponemon)
The Protected Harbor Difference: Our compliance-first engineering approach embeds regulatory requirements into the DNA of your environment. As a SOC 2, Type II certified organization ourselves – a rare and high-value trust marker – we transform compliance from a reactive, costly liability into a proactive, marketable asset that demonstrates your commitment to security and trust.
Failure #3: The Single Point of Failure (SPOF)
The Problem: We consistently find entire operations hinging on one critical component: a single internet circuit, one aging server hosting a key application, or a lone individual who holds all the “tribal knowledge.” When that one point fails, the entire business stops.
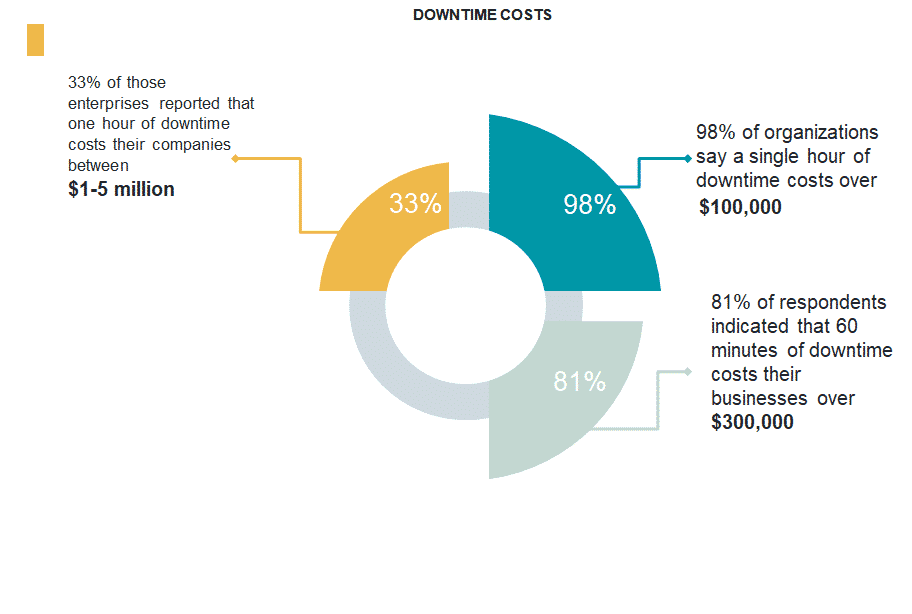
Business Impact: This isn’t merely a technical disruption – it’s complete operational paralysis with immediate financial consequences. One failure means direct revenue loss, halted productivity, and frustrated customers. The financial impact is quantifiable and severe.
According to Gartner, the average cost of IT downtime is $5,600 per minute. That translates to over $300,000 per hour in lost productivity, revenue, and recovery efforts.
The Protected Harbor Approach: We architect for resilience. By designing redundant systems – from internet paths with SD-WAN to failover servers – and proactively cross-training our staff to eliminate tribal knowledge risk, we eliminate SPOFs. We ensure that when (not if) a component fails, your business doesn’t.
 Failure #4: Frankenstein Network
Failure #4: Frankenstein Network
The Problem: Over the years, technology has been added in pieces – a new solution for accounting, a different tool for marketing, a patchwork of cloud apps. The result is a complex, poorly documented, and insecure “Frankenstein’s monster” of a network. No one fully understands how it all connects, making support, security, and scaling a nightmare.
Business Impact: Soaring IT support costs, increased security vulnerabilities, and inability to adapt to new opportunities. It creates technical debt that cripples innovation and drains resources.
The Protected Harbor Difference: We believe in solving the root issue. We start by diagramming your entire network and bridging internal teams to uncover what’s truly in use and how it connects. Then we create a strategic, unified technology roadmap to simplify and standardize your stack, giving you control and clarity.
“Our partnership with Protected Harbor transformed our IT from a constant source of anxiety into a strategic asset. They saw the root causes we’d been missing for years.” -A Protected Harbor Client.
Failure #5: The Vendor Blame Game
The Problem: When you have multiple vendors for internet, phones, software, and hardware, outages become a finger-pointing contest. Your team is stuck in the middle, playing referee while the business suffers. The problem doesn’t get solved; the blame just gets passed around.
Business Impact: Extended resolution times during crises, immense frustration for your staff, and a lack of accountability for the outcomes you’re paying for.
The Protected Harbor Difference: We build long-term, mutually beneficial partnerships – a rarity in our industry. Our partnership model provides unlimited support and single-point accountability. As your primary technology partner, we own vendor relationships and troubleshooting.
Crucially, our contracts include a commitment to proactively reduce issues, not just reactively resolve them, ensuring your business enjoys stable, predictable technology operations.
Case Study Highlight: Proactive Outage and IT Failure Prevention
This is one example of how Protected Harbor transformed a client’s IT from a liability into a strategic asset – a result achievable across any industry.
A multi-location healthcare client was suffering from frequent network outages that disrupted patient care. A typical MSP would have just rebooted the equipment each time. Protected Harbor implemented our 7-Step Outage Prevention Framework.
We diagnosed a root cause that previous providers missed: a complex interplay of bandwidth saturation and a misconfigured router. By solving this and building a redundant, monitored architecture, we transformed their network from a critical liability into a strategic asset for reliable care.
Results:
- 99% Uptime achieved
- 40% reduction in common IT errors and tickets
- Established a Comprehensive Asset Inventory
Conclusion
Avoiding IT failures isn’t enough. The real opportunity lies in eliminating hidden liabilities and turning technology into a driver of growth, resilience, and enterprise value.
That’s what our Strategic IT Liability Assessment delivers:
- A comprehensive visibility audit of your IT environment
- A security gap analysis that pinpoints blind spots
- A compliance readiness review (HIPAA, PCI, SOC 2, or the standards that matter most to your business)
- A customized roadmap to resilient, growth-ready infrastructure
We build long-term, mutually beneficial partnerships – including unlimited support – to ensure your IT is not just stable, but a strategic advantage.
Turn today’s IT risks into tomorrow’s strategic advantage.





 3. Steps to Achieve and Maintain Compliance
3. Steps to Achieve and Maintain Compliance




 IT Updates for Tech Leaders
IT Updates for Tech Leaders

 What To Look for in a Great IT Support Team?
What To Look for in a Great IT Support Team?
 CEOs and company executives are ultimately accountable for safeguarding their organization’s long-term security, which helps mitigate cyber risks. As executives become more aware of risk and security management, they ask increasingly nuanced and complicated leaders questions. At the board level, interest in security and risk management (SRM) is at an all-time high. In
CEOs and company executives are ultimately accountable for safeguarding their organization’s long-term security, which helps mitigate cyber risks. As executives become more aware of risk and security management, they ask increasingly nuanced and complicated leaders questions. At the board level, interest in security and risk management (SRM) is at an all-time high. In  A risk outside the tolerance needs an antidote to bring it within tolerance. It does not require dramatic changes in a short time, so beware of overreacting. The Gartner report presents a way to defend the risk management decision, and you can change it according to your organization’s risk tolerance.
A risk outside the tolerance needs an antidote to bring it within tolerance. It does not require dramatic changes in a short time, so beware of overreacting. The Gartner report presents a way to defend the risk management decision, and you can change it according to your organization’s risk tolerance.