The Biggest Data Risks and Cybersecurity Trends for Law Firms

The Biggest Data Risks and Cybersecurity Trends for Law Firms
In the digital age, law firms are operating within a high-risk environment. The number of cyber-attacks continues to rise, as do the associated costs. Recent studies suggest that, on average, small and medium-sized businesses spend more than $200 million annually on cyber security breaches.
These statistics show just how important it is for companies of all sizes to take cybersecurity seriously as well as highlight the risks involved in working with sensitive data. After all, no company wants their clients’ personal information to fall into the wrong hands.
We are excited to launch our 2022 Law Firm Data Breach Trend Report white paper. This report will be a compilation of data analysis from hundreds of law firms across the globe, as well as interviews with more than 100 partners and senior-level executives from the largest law firms in the US. We have learned a lot from these conversations and are excited to share our findings with you.
Download the white paper for free today!
Protecting Client Data:
The Biggest Challenge for Law Firms
Protecting client data is a top concern for law firms of all sizes. While most firms are diligent in protecting sensitive data and complying with local, state, and federal regulations, some are not.
After being asked to identify their most significant challenges when it comes to safeguarding client data, 58% of law firms cited, “managing the sheer volume of data,” and, “ensuring data is secure,” as their primary concern. These findings make sense if we consider that, on average, law firms store more than 5,000 gigabytes of data. The large volumes of data makes it difficult for law firms to constantly comply with the most up-to-date security protocols.
Top Threats
Your client’s data is constantly in danger from simple breaches, such as those resulting from a stolen laptop to even more extensive hacking schemes.
Here are a few actions you’re probably doing now that can endanger your clients most sensitive information.
-

Skipping Assessments – To help prevent a data breach, an annual inventory should be taken to understand what devices and data you have, where they are located, and who has access to them. It’s also essential to conduct a security and risk assessment. How vulnerable is your information? What would the ramifications be if it was stolen?
- Understaffed and Underfunded IT Departments – A majority of IT departments are usually very understaffed and overburdened with day-to-day work. This leaves little time for them to improve their security infrastructure, as they always react rather than improve.
- Lack of Employee Security Training – Analysts claim that non-malicious attacks are the most common security breach that law organizations face. Unfortunately, many legal companies have failed to adequately train their employees on IT security basics.
- Cloud Migration & Apps – Your business needs to make sure it has a good strategy when it comes time to migrate, including fundamentals like access control and governance, API integrations, and continuous monitoring.
Recent Law Firm Breaches
New York City’s Law Department (July 2021)
Grubman Shire Meiselas & Sacks (May 2020)
Vierra Magen Marcus (May 2020)
Mossack Fonseca (April 2016)
Top Cybersecurity Trends for 2022
Use Password Authenticator – Password authentication is a method in which a user enters a unique ID and key compared to previously stored credentials. It is one of the quickest forms of security; you can set up your device to require some identification before letting someone access it. This can be done using a passcode, PIN, password, fingerprint, or a 2-factor authentication (2FA).
Use Effective EDR – Using effective EDR (Endpoint Detection and Response) tools can help you improve the security of your network by aggregating data on endpoints, including process execution, endpoint communication, and user logins.
Move to a Virtual Server – Moving to a virtual server is essential as it has many benefits that address the security concerns law firms face. These benefits include getting the ability to prioritize critical traffic and improving network agility while reducing the burden from the IT department.
Isolated Backups – A remote or isolated backup is stored separately from other backups and is inaccessible from the end-user layer. Creating a remote backup helps to reduce security breaches, especially ransomware attacks.
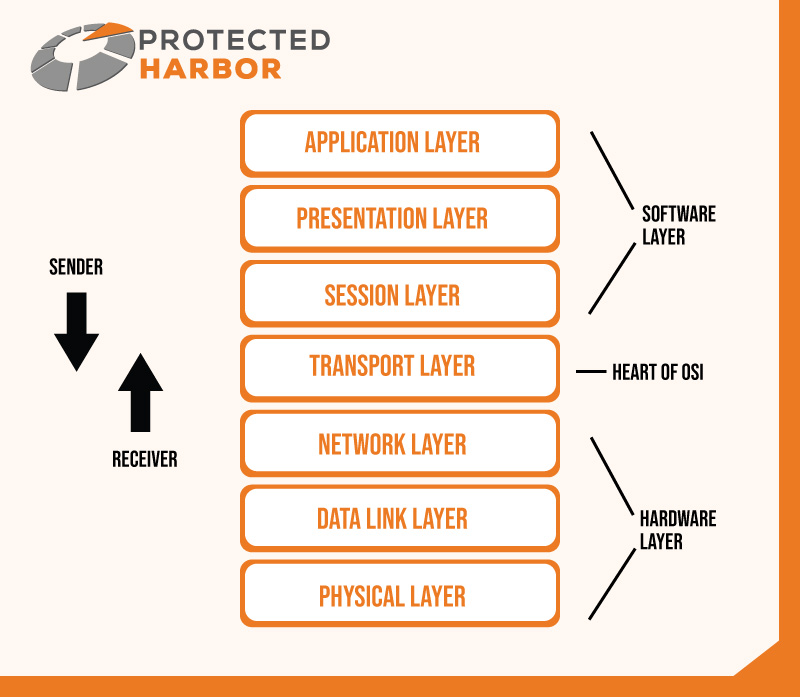
Know Your Network Map – Understanding the network map is critical to complying with data privacy regulations as it provides an overview of devices and data on your network. This overview is crucial in identifying and minimizing the attack surface of a system. It will also uncover devices that IT staff may not know are there—for instance, an old, decommissioned server.
Timely Software Updates – It sounds simple, but vulnerabilities caused by outdated software are a significant problem. Keeping all the software up to date is essential for better performance. It also helps discourage potential cybercriminals who like to take advantage of previously-found weaknesses in software.
Data Encryption – In 2022, law firms must use encryption methods for systems, data in the cloud, data at rest, and data in transit to protect their files. Hard drives, USB devices, and phones should also use encryption if they are holding sensitive data
To read the cybersecurity trends for 2022 in detail, download our free white paper today.
Conclusion
By 2023, 80% of law firms will have experienced a data breach, according to research from LexisNexis. Given the rising number of cyber-attacks law firms face, it is necessary to take cybersecurity seriously. Law firms can better protect their sensitive data against these cyber threats by investing in the latest security technologies.
Protecting sensitive client data is essential for all law firms.
Stay on top of the latest trends and best practices for data security by downloading our white paper today! We highlight what law firms should be doing to protect their data and prevent a breach from ever happening. Protected Harbor also has other resources to prevent a law firm data breach, which you can access free from our digital library.
Keep in touch for more tips on how to keep your company safe from cybercriminals.





 Lack of Multi-factor Authentication for Privileged Users
Lack of Multi-factor Authentication for Privileged Users

 4. Backup User Data in Several Locations and Isolated Backups
4. Backup User Data in Several Locations and Isolated Backups

 ES File Explorer
ES File Explorer
 Most Common Exposure Points for Cloud-based Applications
Most Common Exposure Points for Cloud-based Applications







 Microsoft tweeted that it had determined the downstream effects of Teams integration on several
Microsoft tweeted that it had determined the downstream effects of Teams integration on several 

 Threat Hunting
Threat Hunting

 What are the Benefits of Load Balancing?
What are the Benefits of Load Balancing?