Do I need to permit a VPN? (NO!) – How Can I Transmit Info Confidentially?

Should I Allow a VPN? (NO!)- How do I Send Data Privately?
Do you have sensitive data that you need to send over through email? If so, are you taking the proper security measures when sending them? If you need to exchange files and documents with others online, you want to be able to do so as quickly, securely, and painlessly as possible.
When it comes to sending data privately, you have a few options. The primary way that people do this nowadays is by using a Virtual Private Network (VPN).
According to SurfShark’s data on internet users, VPN usage has been rising gradually worldwide, particularly since the widespread use of smartphones and the rise in certain online activities like business transactions and remote work.
However, some significant drawbacks of VPNs and other methods can cause people to stop using them.
Should You Allow VPN to Transfer Files Securely?
The answer is probably not if you’re using a VPN and want to transfer files from your phone or computer.
Here are some reasons why VPNs aren’t always secure:
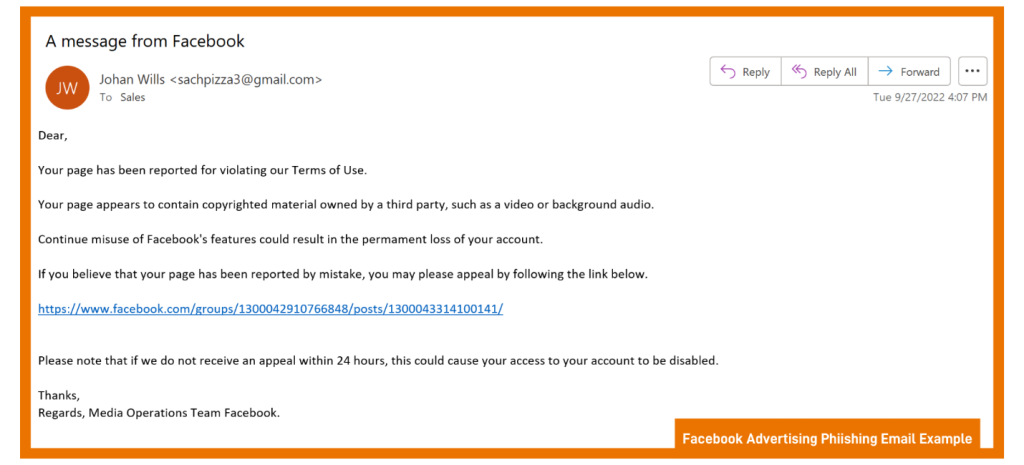
- They can’t create or enforce policies that protect credentials: For example, if you use your Netflix account with a VPN, it might be easier for hackers to steal your login information.
- Lack of accountability: Since VPNs hide IP addresses and locations, it’s hard to know who is behind a particular connection. This makes it harder for law enforcement agencies to track down criminals who use them for illegal activities.
- VPN isn’t legal in all countries: Some countries ban VPN use altogether, while others require users to register with the state before operating.
- No Hacker Protection: It is only a tool that makes your online activity more anonymous and secure. The fact that it hides your IP address and location shows that it has some level of encryption, but it doesn’t mean that your data is encrypted.
- You may experience connection breaks: VPNs can cause connection errors or disconnections, which means your data could be at risk of being intercepted by someone else. You could get kicked out of the VPN for no reason or lose access to your favorite websites if the VPN provider goes out of business.
So, if you want to get work done on your computer while connected to a VPN, don’t do it — even if it’s only for a few minutes. If someone compromises your connection, they can see everything you do online and steal any passwords you use in their system.
 How do I Send Data Privately?
How do I Send Data Privately?
Consider these tips for sending data safely:
1. Only Receive Data Transfer from Trusted Sources
You need to use a trusted source to send and receive data privately. If your device has access to the Internet, it can be compromised by malicious software or hackers.
If a hacker gains control of your computer, they can steal the sensitive information on your device and use it to commit identity theft. A good solution is only to use trusted cloud storage and file-sharing services that work with your operating system.
2. Install Firewall, Antivirus, and Anti-Malware Programs
Firewalls block incoming connections and prevent unknown programs from accessing your computer. The best way to protect yourself from computer viruses is to use a firewall. You can also set up a parental control feature on your computer that blocks access to adult sites and websites with inappropriate content.
3. Use Trusted Cloud Storage and File Sharing Services
For this purpose, you can also use trusted cloud storage services like Dropbox or Google Drive. These services provide end-to-end encryption for all files uploaded through their servers so that only the person who uploaded them can access them. This is much more secure than sharing folders or other cloud storage services that might allow anyone on the Internet to access your files anytime because those sources are not encrypted!
4. Encrypt Your Files Before Transferring Them to Other Devices
Before sending any sensitive data files, such as financial information or social security numbers, outside your organization, consider encrypting them using file encryption. File encryption is a method used by many organizations to protect sensitive data files like financial documents and social security numbers from being accessed by unauthorized users.
When encrypted, these files cannot be accessed by anyone other than the person who created them or has physical access to the device that was created (e.g., a USB flash drive). This prevents outsiders from seeing or accessing these files, which could cause significant problems if they become compromised or stolen by someone else.
5. After Transferring, Turn Off the Wireless Connection
If you have a wireless network, it’s possible that your transfer could be interrupted by someone else who is using the same network. Turning off your wireless connection immediately after the transfer is complete will prevent anyone else from stealing your information.
If you’re using a wired connection instead of a wireless one, anyone who manages to tap into the line between you and your computer will be able to steal any data sent over it. The easiest way to avoid this is to use a password when logging into any servers that might contain sensitive information.
6. Use Open-Source OS to Transfer Data Safely Using Physical Media
Using an open-source OS, like Linux, can be very helpful in reducing the danger of transmitting malware into your computer when transferring sensitive and crucial data between devices, such as when using a USB stick or other physical media.
This is because most viruses and malware cannot be executed on your machine. After all, the open-source OS prevents them from doing so. Before the transfer procedure, the harmful files will go inactive, and you can quickly delete them.
Final Words
There are numerous reasons to use a VPN service, but the pros do not necessarily outweigh the cons. If you value privacy, there is no reason to let a Virtual Private Network or any other service send your data through an unencrypted channel. It’s better not to use a VPN and to switch to other secure sources to transmit data effectively and privately.
Other options are available such as Google Drive and Cloud services, they are just as easy to use and have better outcomes.
Protected Harbor data protection service secures data and sends it privately, so your data remains, well, private. It offers a security-first approach to data transfer, making it the best option for enterprises to transfer their sensitive data.
This service secures your network endpoints plus keeps your data secure by encrypting it before it ever leaves your network. Finally, it meets the standards for compliance with regulations like GDPR. It’s a secure and easy-to-use service that can be implemented quickly with a simple click-to-send button.
Moreover, it permits only authorized personnel to access the data, which is critical for enterprises. If you are looking for a best-in-class cloud solution, choose a trusted service like Protected Harbor.
Consult with our data security expert today to learn how we keep your data safe.












 Keeping Your Passwords Safe and Protected
Keeping Your Passwords Safe and Protected




 How to Prevent Data Theft from Employees?
How to Prevent Data Theft from Employees?





 According to the researchers, the questioned apps include radio tuners, e-banking, city transportation, and similar sites, each receiving between fifty-thousand and five-million downloads.
According to the researchers, the questioned apps include radio tuners, e-banking, city transportation, and similar sites, each receiving between fifty-thousand and five-million downloads.