Real Estate Sector in Suffolk County Destroyed by Cyberattack
Suffolk County Real Estate Industry Crushed by Cyberattack
Following a cyberattack on the Suffolk County government earlier this month, real estate transactions have come to a halt.
Since the cyberattack more than 20 days ago, verifying property titles and filing paperwork has been challenging, which has abruptly halted all deals in the county, according to The Real Deal. On September 8, The Suffolk Times reported that a breach by a group known as BlackCat knocked down county websites, servers, and databases.
It’s been stressful for real estate professionals in the New York area. While this may seem like just another insignificant cybersecurity issue, the implications are much deeper than we can see. In this post, we’ll dive into what happened, why it’s so concerning, and how to stay safe.
What Happened?
The Suffolk county cyber attack crippled the county clerk’s office, which is in charge of documenting paperwork and assisting with records searches for properties, and shut down the county’s internet systems last month.
Due to title companies’ inability to accurately scan county databases to confirm that the properties don’t have any liens, judgments, or other encumbrances to pass title, real estate closings have been postponed or canceled, especially on larger commercial acquisitions.
According to attorney David Rosenberg of Garden City-based Rosenberg Fortuna & Laitman, “After the Suffolk county hack, delay in restoring access to the county’s real estate records, which had been available online before the hack, is causing many title companies to withhold final clearance that would allow closings to occur.”
The ability to ascertain whether new liens, encumbrances, or property transfers have been recorded between the first title report and the closing depends on these documents. In more recent deals, it causes the title company to postpone the initial title report, which makes it impossible for lawyers, purchasers, borrowers, and lenders to close any sizeable transactions confidently.
According to The Suffolk Times, a hacker collective known as BlackCat took responsibility for the suffolk county data breach and demanded payment to allow users back into government servers. The hackers say they have taken four gigabytes of information, including information on specific citizens, from the clerk.county.suf domain.
What this Means?
Deals have slowed to a trickle since neither banks nor buyers can confirm that titles are clean — that is, the property is free of liens and that the seller is the legal owner and only owner — without checking the property out on county websites.
The process of filing claims is another problem. While some records supplied by hand are being accepted and preserved in chronological order, they won’t be officially on file until the systems are operational. Since New York is a “rush to record” state, the first party to file a title claim is the one whose claim is considered; hence incorrect document filing could result in significant issues.
According to Attorney Howard Stein, head of the Real Estate Practice Group at East Meadow-based Certilman Balin Adler & Hyman, the damage will increase exponentially. “New title reports cannot be created, and as a result, newly signed transactions are completely blocked.” The economic implications could be disastrous if a solution cannot be found.
Some title insurers have been forced to add an exception to their Schedule B list of things they cannot insure due to the closure of county systems. This exception now states that they will not cover “any defect, lien, encumbrance, adverse claim, or other matter created by or arising out of the inaccessibility of the Office of Suffolk County, including, but not limited to, an inability to search the public records, or any delay in recording of documents in the public records.”
According to Linda Haltman of Plainview-based Hallmark Abstract Services, “If they were in process before the hack and all of the title searches were done, they have been closing,” “Underwriters are letting sellers sign affidavits if the searches have already been conducted, with the exclusion of unoccupied land, new development, and foreclosures.”
Haltman warns that delays in closing can become costly given the fast-increasing mortgage rates.
“Delays in being able to close could be costly without an extension of a rate lock-in term,” she warned. “It could cost an extra $5,000 upfront to pay down the rate on a mortgage for a $500,000 house.”
 Protected Harbor’s Take on the Matter
Protected Harbor’s Take on the Matter
On September 8, websites and web-based apps for Suffolk Government were shut down after officials discovered malware in county systems. Images of county documents were posted as ransomware on the website DataBreaches.net. The hackers claimed to have taken court records, sheriff’s office records, contracts with the state, and citizen personal data from the county clerk’s website.
“An immediate resolution to this issue is critical, as there will be an increasing number of damages as a result of the shutdown,” Protected Harbor CEO Richard Luna said.
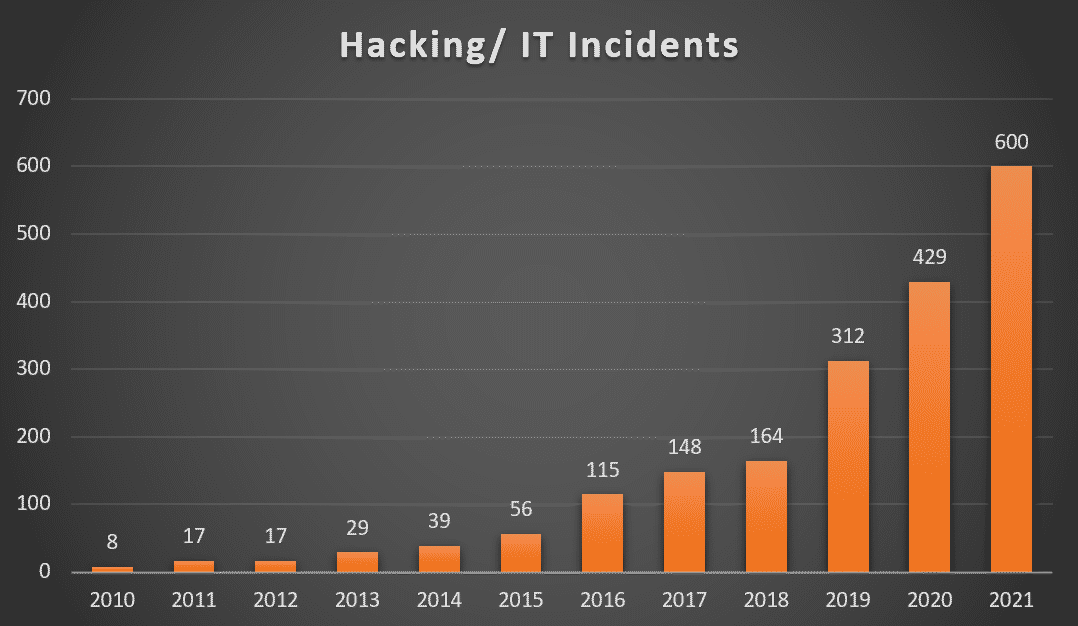
Earlier, most small and mid-sized enterprises were unaware of the importance of cybersecurity. However, with the increasing number of cyber-attacks, it has become imperative for all enterprises to invest in cybersecurity. As a company that provides enterprise-grade software, we have always ensured that all our products are secure.
Tips to Fight Against Ransomware
-
Desktop/Network & Backup Isolation
The first step in a new network design is to limit through segmentation of the network. Desktops, Servers, and the backup should all be on separated and isolated networks. Using this approach, an infected desktop will not be able to access the backups and will not infect the backups.
-
Virtualization
We can accomplish desktop and network isolation using virtualization. Virtualization allows you to back up the entire desktop, not just shared folders, databases, or scanned folders, but all folders. This means we can recover the whole office, and not pieces of the office.
-
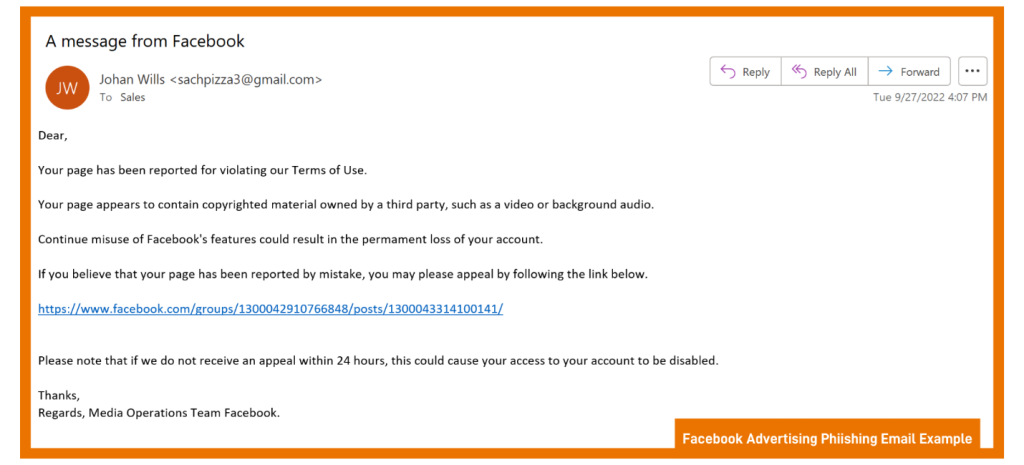
Email & Web Filtering
Filtering email and web content is an integral part of the Ransomware defense. Good email filtering should include pattern recognition. The initial Ransomware attacks follow a template, and when properly configured, email filtering systems block or quarantine the attack.
-
Enable network monitoring
Network monitors can alert and warn on unusual traffic or traffic that is typical of an attack; for example, if specific information is transmitted out of the network, that would trigger an alert.
-
Geo-Blocking
Maintain enhanced network protection that includes active parameter checking and Geo-Blocking. For example, check the address of inbound requests, and if the IP is from a blocked country, then the traffic is blocked even before it reaches the client’s network.
Continue to read in detail how to protect yourself against ransomware attacks.
Final Thoughts
Cyber threats are increasing daily, and it is essential to stay protected against them. It is impossible to avoid cyber threats altogether, but we can stay protected by following specific steps and implementing the best cybersecurity practices.
Protected Harbor offers a range of cybersecurity products and services that protect your business against all types of malware, ransomware, and other cyber threats. It also ensures data integrity, regulatory compliance, and system availability.
The Ransomware solution is highly scalable and can be deployed on-premises or in the cloud. It is easy to set up and maintain, with no technical skills required. The solution comes with a 24/7 support team that will resolve any issues quickly and efficiently. We are committed to protecting all types of businesses and organizations, offering products and services that are both affordable and easy to use.
We believe there is no better time than now to invest in cybersecurity, as it is the only way to stay ahead in this highly competitive and ever-changing digital world. October is our Annual Cybersecurity Month; we’ll be posting security blogs and videos to keep you protected. Get in touch with our expert and get a free IT Audit today.





 Keeping Your Passwords Safe and Protected
Keeping Your Passwords Safe and Protected







 Businesses are not reacting promptly to malicious activities. Technology is constantly and rapidly evolving and expanding the attack surface in multiple ways. At the same time, cybercriminals are adapting advanced courses and escalating the threat landscape. They are adopting sophisticated ways to attack, and the struggle to deal with the changes is real. Malicious or unauthorized activities occurring inside your network are causing damage without even you knowing that. How can you detect those malicious network activities inside your network as quickly as possible and respond efficiently to avoid or reduce the potential damage?
Businesses are not reacting promptly to malicious activities. Technology is constantly and rapidly evolving and expanding the attack surface in multiple ways. At the same time, cybercriminals are adapting advanced courses and escalating the threat landscape. They are adopting sophisticated ways to attack, and the struggle to deal with the changes is real. Malicious or unauthorized activities occurring inside your network are causing damage without even you knowing that. How can you detect those malicious network activities inside your network as quickly as possible and respond efficiently to avoid or reduce the potential damage? Best practices to prevent malicious activities in a network
Best practices to prevent malicious activities in a network

 After the coronavirus outbreak, everyone is doing their
After the coronavirus outbreak, everyone is doing their  Tell Employees to use Two-Factor Authentication.
Tell Employees to use Two-Factor Authentication.



 Patient Data Theft: High risk
Patient Data Theft: High risk