Ransomware Risk Is Designed

Ransomware Risk Isn’t Random — It’s Designed by Your Environment
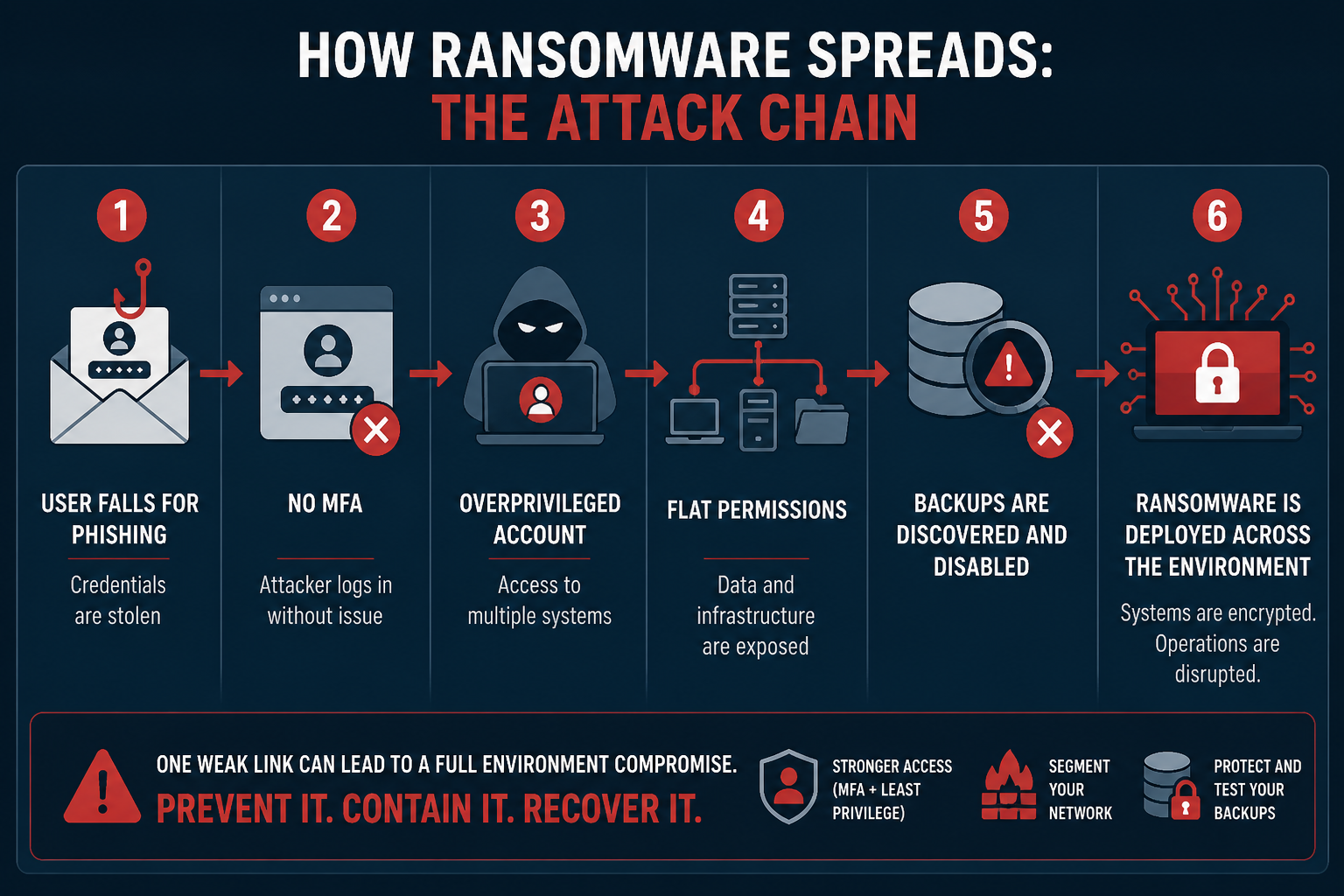
Most cyberattacks don’t need to rely on advanced exploits. Many successful incidents rely on exploiting predictable, preventable internal weaknesses. Attackers don’t need to outsmart your defenses — they can just look for:
- Weak or missing authentication controls
- Excessive access once inside
- The ability to destroy recovery options
These are not edge cases — they’re common operational gaps. Ransomware success isn’t about how advanced the attacker is — it’s about how exposed your environment is. Ransomware doesn’t succeed because an attacker got lucky. It succeeds because the environment allowed it to succeed. Ransomware follows the path you’ve already built. Attackers don’t need to create complexity when they can just exploit what’s already there.
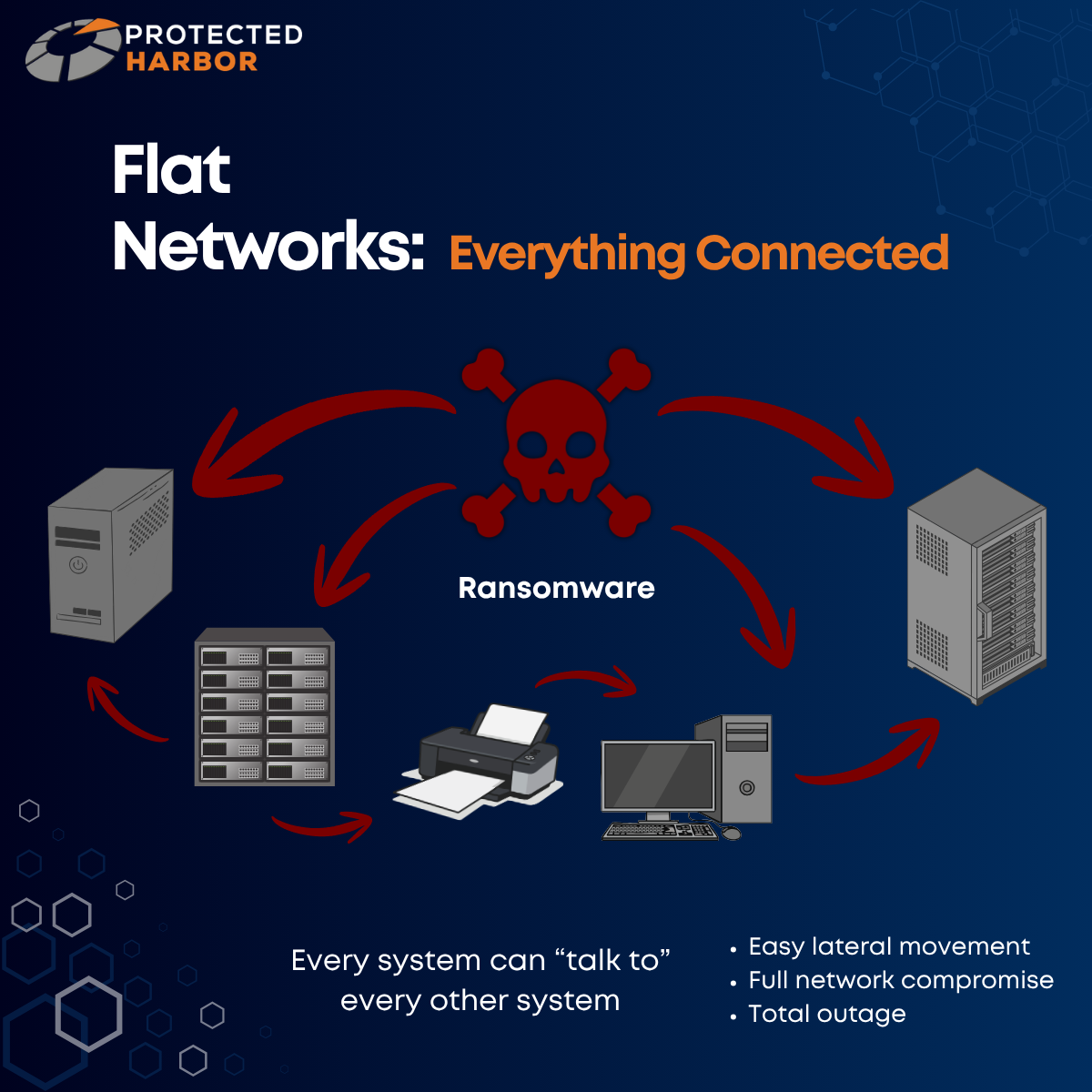
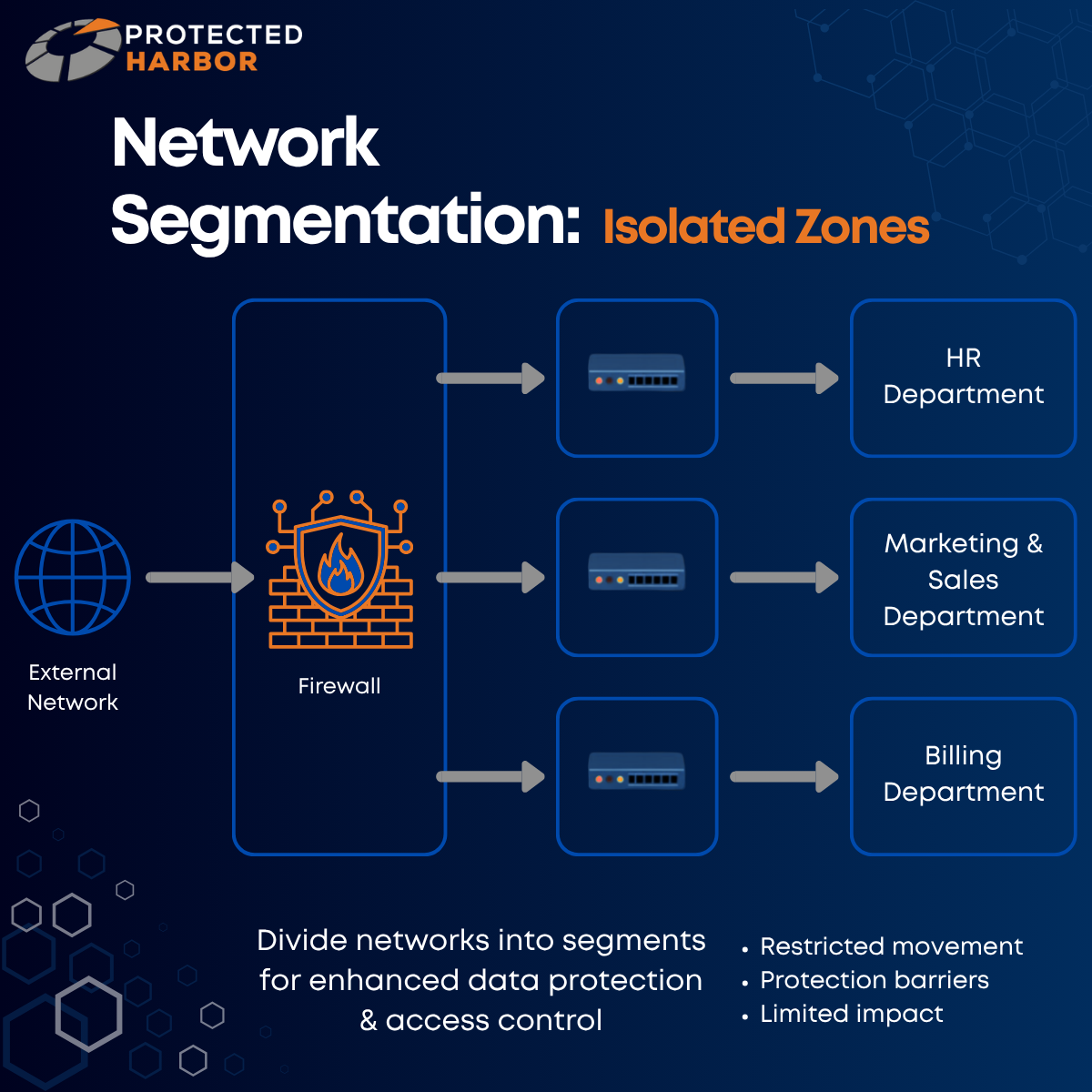
In our previous blogs, we looked at how mixed-use servers and flat networks increase your vulnerability to ransomware. In this blog, we are going to focus on common identity/ access weaknesses, and why protecting your backups is one of the most crucial ways to save your business.
The Keys to the Kingdom
Organizations must properly manage user accounts and be mindful of excessive permissions. If one account can access everything, one compromise can destroy everything. Mismanaged accounts and permissions can look like:
- Users with access far beyond their job function
- Service accounts with domain-level privileges
- Shared admin credentials across teams
- Wide-open file shares
- Dormant accounts still active
Many environments evolve over time without governance, which can lead to permission creep, forgotten accounts, and inconsistent access policies. These issues also occur when an organization is coordinating multiple vendors and there is no clear ownership. Once an attacker gains any valid credentials, they can blend in as a legitimate user, avoid detection by security tools, and move faster than traditional defenses can react.
If an attacker obtains access to an ‘overprivileged’ account, you’re essentially giving them the keys to the kingdom. This broad access means attackers don’t need to hack your systems to wreak havoc — all they need to do is log in.
Once in, attackers will:
- Use stolen credentials to access multiple systems
- Escalate privileges using misconfigurations
- Move laterally without triggering alarms
- Quickly access sensitive data and critical systems
Authentication = trust. If identity controls are weak, attackers can inherit that trust.
Hidden Risks & How to Prevent Them
Hidden risks include:
- Dormant accounts: Old employees, contractors, test accounts.
- Shadow IT: Accounts created outside of IT oversight.
- Lack of access reviews: Permissions are never reevaluated.
- Flat directory structures: No separation of privilege tiers.
- Wide-open share permissions: “Everyone” or “Domain Users” can access critical shares.
All of these risk factors create an easy staging ground for ransomware encryption.
What to do instead:
- Enforce least privilege (only what’s needed, nothing more)
- Conduct regular access reviews
- Automate processes for employees who join, move, or leave
- Segment administrative roles
- Lock down shared resources with clear ownership
Ransomware Doesn’t Need to Break In — It Logs In & Spreads
Let’s see an example. An organization tends to be lax with their permissions, but their security is otherwise strong. A user unknowingly clicks on a malicious link, introducing malware into the environment. Once inside the environment, the attackers focus on getting access to local admin so they can extend that access to the entire deployment. This is known as escalation of privilege. If the organization does not utilize deep monitoring, they might not be alerted to suspicious activity in their environment. By the time they realize, it may already be too late. Once an organization is locked out of their deployment, an attacker may deploy ransomware or scan the deployment for sensitive information (e.g., social security numbers, payment information, files that contain keywords like ‘password’ in the name).
Attackers always target data because data is currency. Once your data is within their grasp, they can steal it, sell it, hold it for ransom — your entire organization will be jeopardized.
The Open Door Problem
Passwords alone are not enough. This is because passwords are often reused across systems, easily phished, and frequently exposed in breaches. Attackers heavily rely on phishing campaigns, credential stuffing, and password spraying because these methods require minimal effort with a high success rate.
Multi-factor authentication (MFA) introduces a second factor, creating a barrier than can block most automated attacks. Even if credentials are compromised, attackers can’t log in without the second factor (for example, validating a log-in attempt with an authenticator app). Without MFA, stolen credentials are often all attackers need: you’re leaving the door open for hackers to walk right in.
MFA isn’t a silver bullet, but it can stop the vast majority of opportunistic attacks. Using MFA isn’t about being unbreakable, it’s about:
- Increasing effort for attackers
- Reducing attack success rates
- Creating additional detection opportunities
Roll out MFA for email systems, remote access (VPNs), and administrative accounts. App-based authenticators should be used over SMS when possible. Risk-based/ adaptive MFA takes this a step further by evaluating the circumstances around a login attempt (device posture, location, IP reputation, login behavior, etc.) before granting access. It’s also key to educate your users so that they know to never approve unexpected prompts.
The Final Line of Defense
The harsh reality is that modern ransomware doesn’t just encrypt data, it targets backups first, disables recovery mechanisms, and exfiltrates data for double extortion. Common backup mistakes include:
- Backups connected to the same domain
- Always-online backup systems
- Shared credentials between production and backup environments
- No immutability
Backups are your last line of defense — these mistakes make backups discoverable, accessible, and destroyable.
When backups fail, downtime increases dramatically, ransomware pressure rises, and recovery becomes slow, partial, or impossible. A strong backup strategy looks like:
- Immutable backups: Cannot be altered or deleted.
- Offline/ air-gapped copies: Not accessible from the production network.
- Separate credentials/ domains: Limits an attacker’s access.
- Multiple backup tiers: Onsite + offsite.
- Testing: Many organizations perform backups regularly, but never test restores.
Testing is one of the most skipped, and arguably most critical, steps. Testing is key for verifying data integrity, ensuring systems can actually be rebuilt, identifying gaps in the recovery process, and reducing panic during real incidents. A backup that hasn’t been tested is an assumption — not a solution.
From One Login to Total Shutdown
The critical business reality is that organizations who cannot recover quickly lose significant revenue, lose customer trust, and if the attack is bad enough, have to shut down entirely. This is why a multi-layered approach is crucial for protecting yourself against cyber threats. You want to ensure that if one layer of protection goes down, the others will be there to hold the line of defense. If not, you’re completely exposed. Organizations must understand that implementing layers of defense doesn’t happen randomly, it has to be designed.
Flat networks, mixed-use servers, mismanaged permissions, missing MFA, backup mistakes — these failures don’t happen by accident. Implementing layers of protection takes conscious thought, planning, and effort. That is why it is so important to have infrastructure that is application-aware and built with security top of mind. Individually, each of these failures are risky. Combined, they create a near-guaranteed path to full business disruption.
No single failure causes the breach, but the damage can be catastrophic when you lack:
- Layered defenses
- Containment
- Recovery capabilities
The Protected Harbor Difference
Application-Aware Infrastructure: Designing for Outcomes
Security decisions aren’t neutral — they actively shape your risk. You’re not simply defending, you’re designing outcomes. All of the weaknesses we have discussed are predictable and preventable. Your environment determines the outcome before the attack starts. Treating security as an afterthought won’t put the odds in your favor in the face of an attack.
At Protected Harbor, we know security isn’t just about stopping attacks, it’s about controlling what happens when an attack occurs, not if.
Your environment determines:
- How far an attacker can go
- How fast they can move
- Whether you can recover
Ransomware isn’t unpredictable. It’s opportunistic. The opportunities it finds are the ones built into your environment through decisions made long before the attack.
Protected Harbor provides Application-Aware Infrastructure in line with Zero Trust principles. Application-Aware Infrastructure is designed, operated, and optimized with a deep understanding of the application’s needs by one accountable partner. This includes:
- 24/7 deep monitoring and custom dashboards
- Isolated, immutable, and tested backups
- Elevated disaster recovery options
- MFA/ role-based access everywhere it matters
- SOC Type 2 certification
- Battle-tested incident response plans
Security failures happen when no one plans for outcomes and owns the infrastructure end to end. We design the infrastructure, proactively manage environments, and own the outcome. One partner. Complete accountability. Total confidence.
Framework: Is Your Organization at Risk?
Ransomware attacks feel sudden — but their success is usually the result of long-standing gaps. Weak identity controls, missing authentication layers, fragile recovery strategies — these are small gaps that compound into big risk. Environments with multiple weaknesses are not the result of bad luck, they are systems designed for failure. Organizations don’t need perfect security, but every control you add slows attackers down, limits access, and reduces the impact.
Application-Aware Infrastructure ensures your infrastructure is built around the specific needs of your application, including and especially in regard to security. The difference between disruption and disaster is rarely the attack — it’s the preparation. Building infrastructure with intentionality is the best preparation you can get.
Consider:
- Do all privileged accounts and critical systems require MFA?
- Are any user accounts ‘overprivileged’?
- Are dormant accounts regularly removed?
- Are backups isolated from your primary network?
- Have you tested recovery in the last 6-12 months?
Contact our team for a complimentary Infrastructure Risk Assessment where we will evaluate your environment and identify:
- Lax permissions
- Weak or missing MFA
- Backup vulnerabilities
- Ransomware blast radius risk
- Performance bottlenecks tied to infrastructure design
- Additional areas of vulnerability
No obligation — just clarity on where you stand.










 6. Cloud Security Becomes Paramount
6. Cloud Security Becomes Paramount




 Detecting Zero-Day Vulnerabilities
Detecting Zero-Day Vulnerabilities